Everything of value has a cost. The same applies to security!
I recently flew to Berlin for business purposes with a known airline. As I was the first one checking in, I was asked if I want the seat near the emergency exit. This is, usually, the place where you have more space for your legs. So, I said without thinking too much: Yeeess, please :).
The plane was a very small one with propellers and the emergency exit was actually the first seat (1 A). Just in front of the cockpit and face to face with the flight attendant.
Now, if you wonder what this has to do with the title of the post, here comes the cost for it:
The flight attendant requested me to take the brochure with the special instructions and read it all. In front of her. It wasn’t much, just two pages, so no big deal.
But, then because she was staying in front of me, watching me directly, she kept making observations and requests during takeoff and landing:
- I am not allowed to put the newspaper on the seat near me because it could fall on the floor and if there is an emergency, someone could slip on it. I had to keep it during takeoff and landing in my hands.
- I have to watch and listen (for the thousandth time) the instructions with the lifevest. I was trying to read a part of the newspaper, but she actually stopped the presentation and looked at started to stare at me. I had to stop reading and pretend that I am interested in what she was showing there. I know it is was not polite of me to do that, but seriously, I watched that so many times that I would be able to recite it.
- I was the last one getting the snacks and the drinks (and I was really, really thirsty)
- I had to shut down the phone where I was ready an eBook ( I never do that, I just put it in Flight mode )
How does this apply to cyber security and privacy?
There is a balance between security and everything else.
The list includes:
- usability : you might have to do some things differently if you want to operate the product/device securely. Think of two-factor authentication.
- features : some features might be blocked or removed if they are not secure enough. Of course, there have to be minimum security requirements defined.
- logic : even if this translates at the end to the first two items, the logic of the product might have to be altered because of security and privacy requirements. The best example is Amazon: as a logged in user, your entire browsing is logged so that you’re shown relevant products based on your interests.
- additional non-functional features must be added: if you’re in a startup like I am, you will have to think twice for every features you add in your product. For raising the bar of your product’s security, you will be forced (by yourself or by legal requirements) to implement features that don’t bring a direct value to the user. But think of what would happen when not implementing those non-functional features!
- delays in delivery: if you want security, you need to test for the lack of it. Testing security is not trivial and requires special knowledge.
There are many more items to be added here, but in the end they resume to those mentioned above.
Solution
Plan for security and privacy costs from the beginning.
Don’t let your plan and/or backlog and your cost structure to be altered at a later point in the implementation because you discover security issues during testing or rollout.
In other words, make sure you add a perceived value to those non-functional requirements.
You can’t make them functional requirements, but you can make their value so heavy that nobody will be able to lower their priority.
Here is a nice presentation about non-functional requirements.
Going back to the “Everything of value has a cost. The same applies to security!”
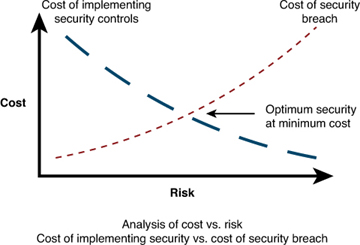
Security has a value, but that value is most of the time a negative value. This means that if you don’t include security controls, you will have to pay, sooner or later, that value.
How to make heavy requirements?
Explain the risk or cost of not implementing that non-functional requirement.
Imagine that your company creates their own webshop to replace a very good and expensive system that was costing the company too much to operate.
Example of a generic non-functional feature:
As a product owner,
I want that the webshop is able to support at least 1000 concurrent users (same as the old system),
So that we can ensure that enough users can purchase simultaneously.
Of course that the owner of the project will complain that such an amount requires additional hardware and so on.
But if you add something like this, he will be thankful that you saved his job:
Additional details:
Failing to achieve this amount of users would mean a drop of 25% in sales in the next holiday season when many users rush to purchase last minute presents.
And here we go: this feature will have no a very high business priority because no one wants to be blamed that the revenue was affected by this new software.
Disclaimer or Keep it decent
I am not suggesting here by any means to lie in order to add security controls or other types of non-functional requirements.
Note that if you lie or exaggerate, sooner or later it will be detected and then you will lose your credibility and obtain the exact opposite effect (and maybe your job as well).
PS:
Regarding the beginning of the email with the seat choice.
I will never blindly accept again that great seat which is good for my legs.
First I will ask which kind of plane that is and then I might accept it.
© Copyright 2015 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca on Cybersecurity
Check www.endpoint-cybersecurity.com for seeing the consulting services we offer.
Visit www.itsecuritynews.info for latest security news in English
Besuchen Sie de.itsecuritynews.info für IT Sicherheits News auf Deutsch