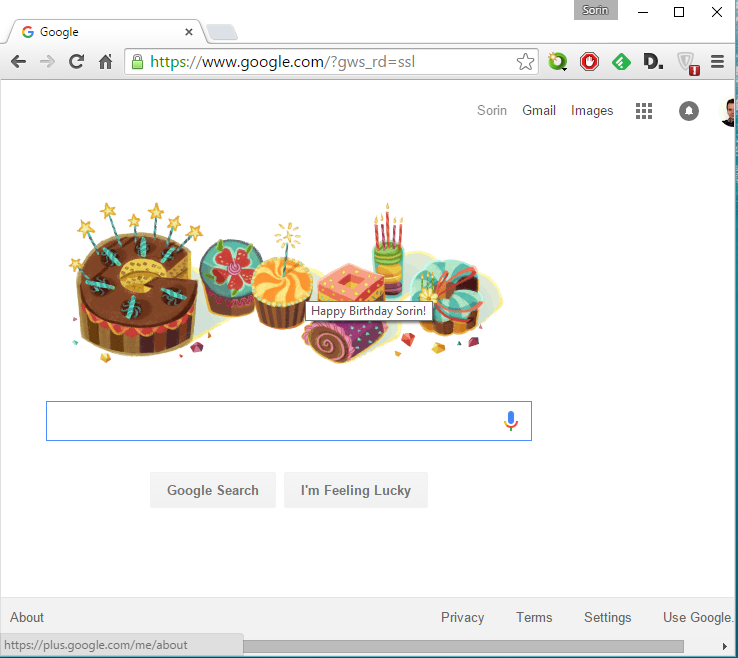
Another Google Support Phishing? No…
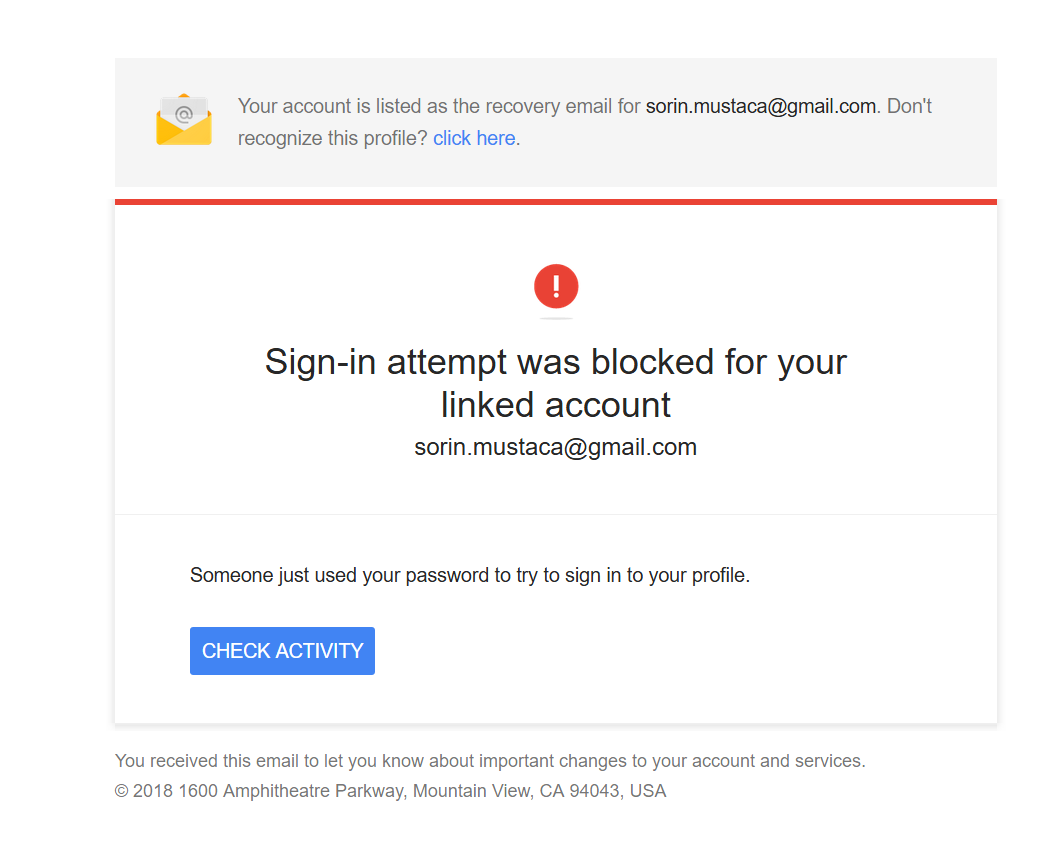
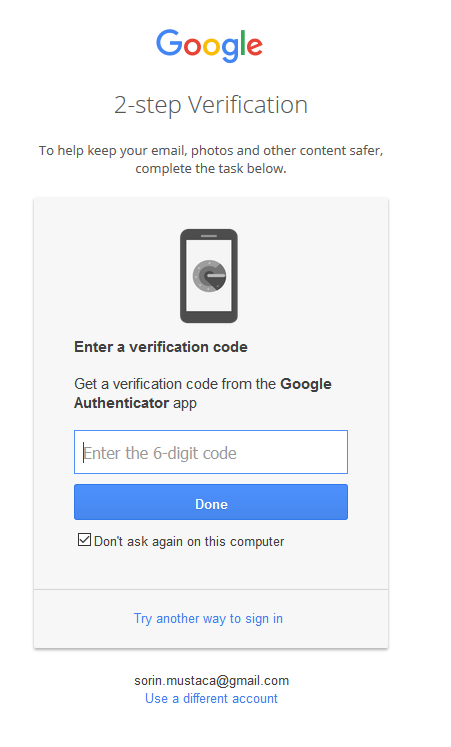
The email below looks like a classical phishing trying to fool users to enter their details and get access to the Google account. But, if you check it, you will be redirected in two steps to an online Canadian pharmacy website. I wonder why so much trouble for a stupid Canadian pharma website? Do people […]