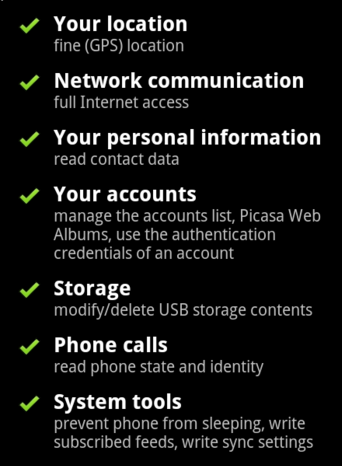
If an App requires some permissions like Access Camera, Access Microphone, does it mean that they can do with these devices of a smartphone whatever they want, whenever they want?
Short answer
Yes, but it is not so simple
Long answer
There are rumours, that apps like WhatsApp, Facebook, G+, etc., are using the camera and microphone to spy on users, even when the device is in idle mode or when the app is not running in the foreground. It was also stated that exactly this was part of their EULAs and hence a legal procedure.
This is Google’s permission for “android.permission.CAMERA” / “android.hardware.camera2” and reads as such:
“Allows the app to take pictures and videos with the camera. This permission allows the app to use the camera at any time without your confirmation.”
all those statements are theoretical assumptions. They are possible to be implemented, however, these apps will never do that.
This doesn’t mean that there are no apps that do exactly this. But, this is the exception and not the rule.
Be careful
If an app requires too many permissions, or if it requires permissions that it should not need, then it is something strange there.
For example, an app that play music doesn’t need to send SMS or read email or make phone calls.
© Copyright 2016 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca on Cybersecurity
Check www.endpoint-cybersecurity.com for seeing the consulting services we offer.
Visit www.itsecuritynews.info for latest security news in English
Besuchen Sie de.itsecuritynews.info für IT Sicherheits News auf Deutsch