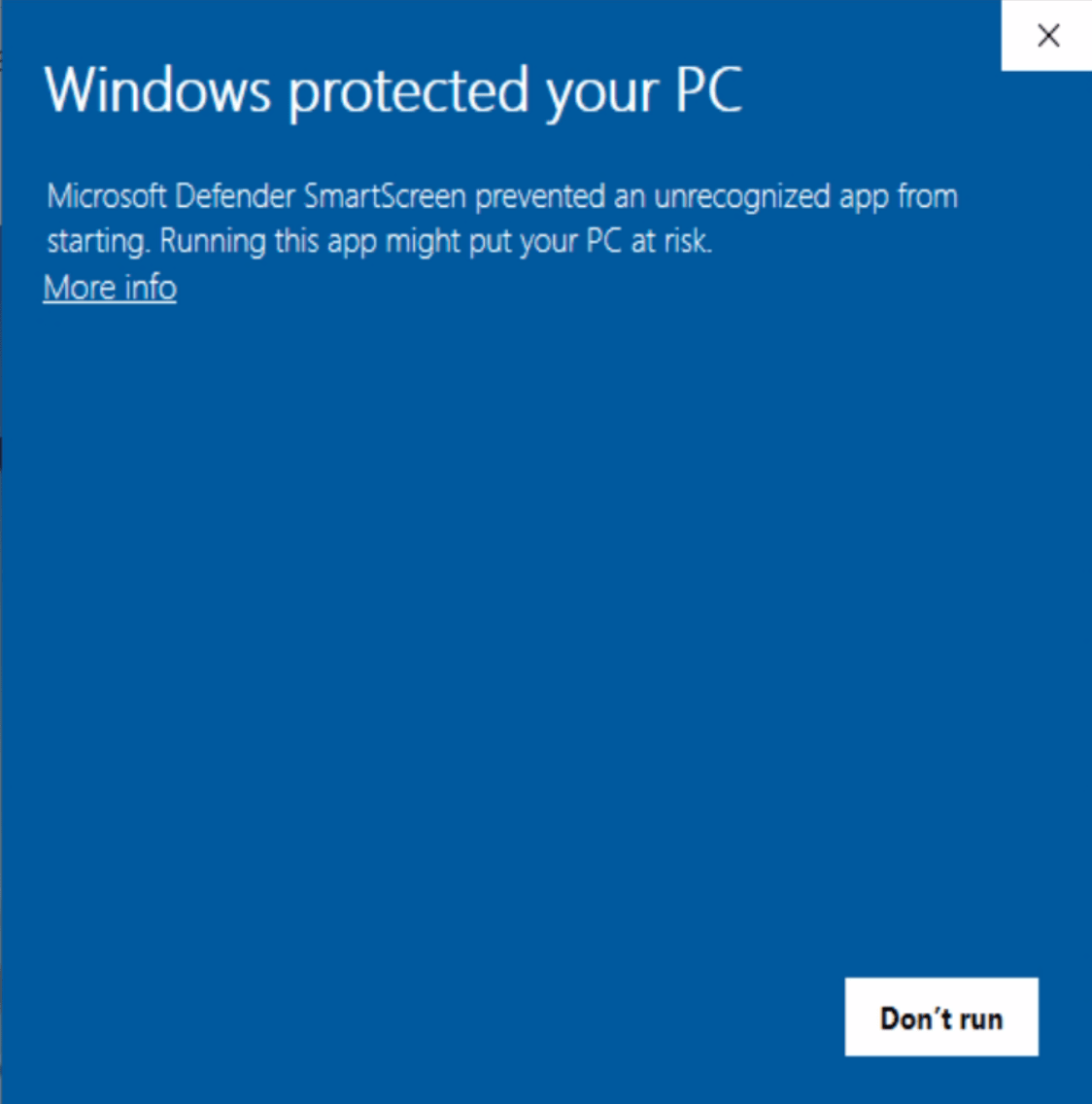
Defender Application Control or Defender SmartScreen – what can you do to not be blocked by it
Ever wondered why do you get one of these popups for your Windows program, despite of the fact that it is signed with a standard code signing certificate ? Applications that are signed with a standard code signing certificates need to have a positive reputation in order to pass the Smart Screen filter. Microsoft establishes […]
You must be logged in to post a comment.