Software engineers, you’re measuring the wrong things. Here’s what actually matters.
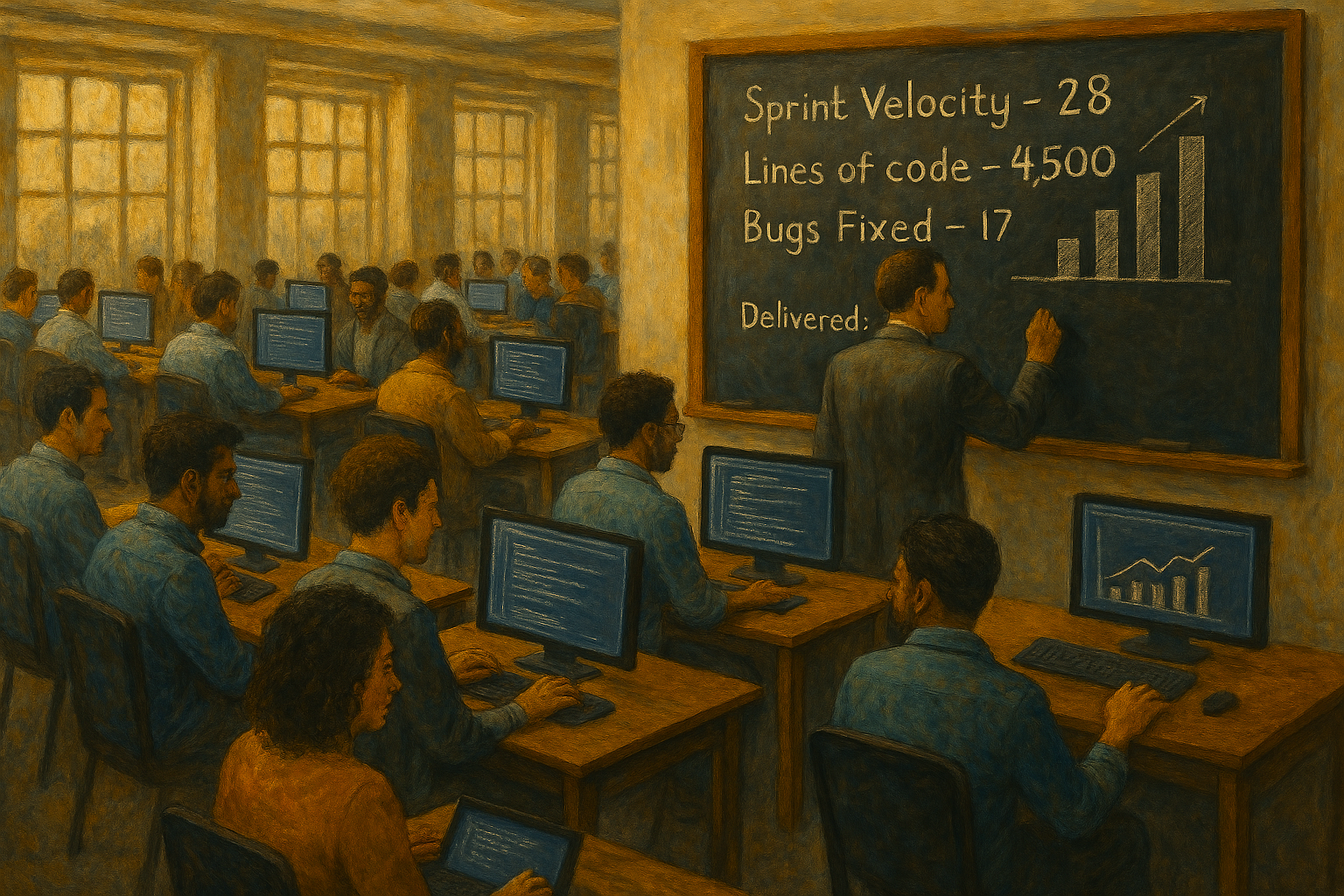
What are you doing is wrong! Most engineering teams are tracking effort and calling it progress. Story points, commit frequency, PR cycle time, items from a Definitions of Done implemented or respected — these are process metrics dressed up as productivity metrics. They tell you how busy your team is. They tell you almost nothing […]
You must be logged in to post a comment.