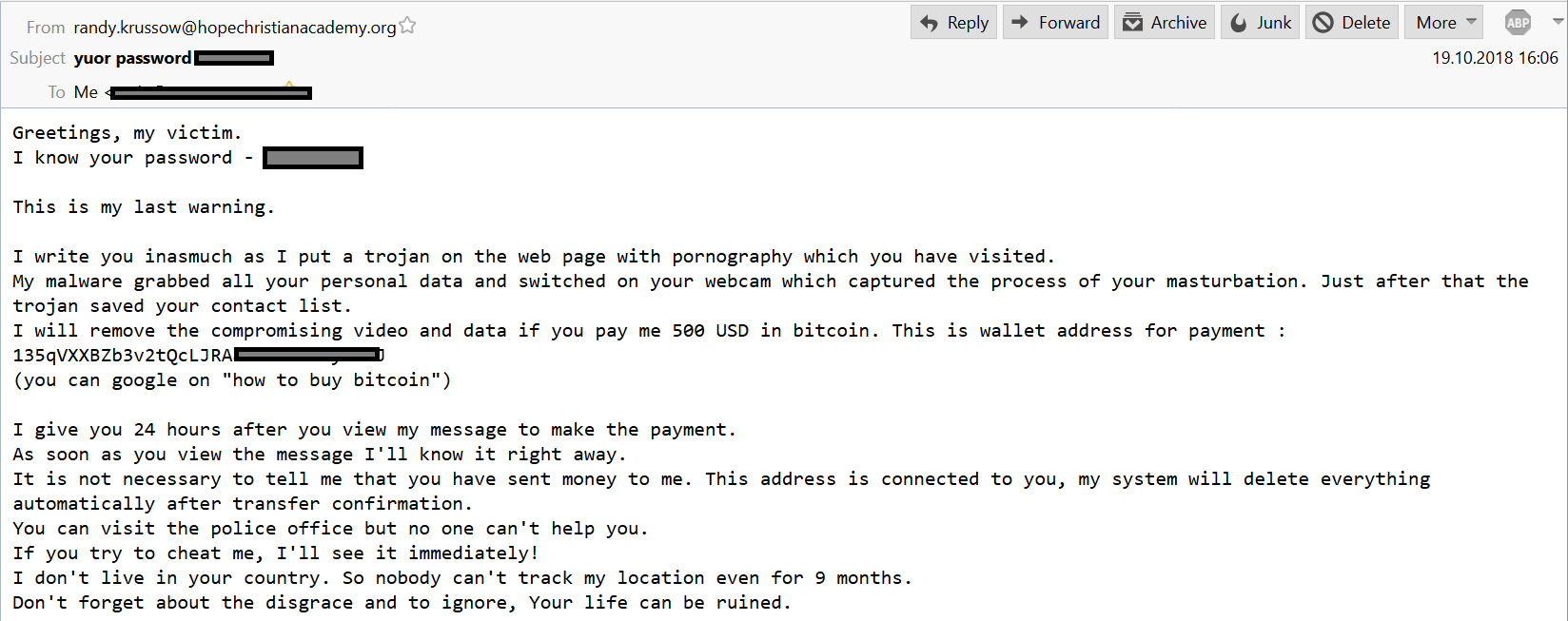
Sextorsion with “real” data – Do not pay!
If you have received an email with the subject “Yuor password – ”, don’t freak out immediately. Yes, the “yuor” is written wrong, but this is how the fraudsters wrote it, not the author of this article. The fraudsters have used a dump with the email addresses and passwords from some hacked website, where you […]
You must be logged in to post a comment.