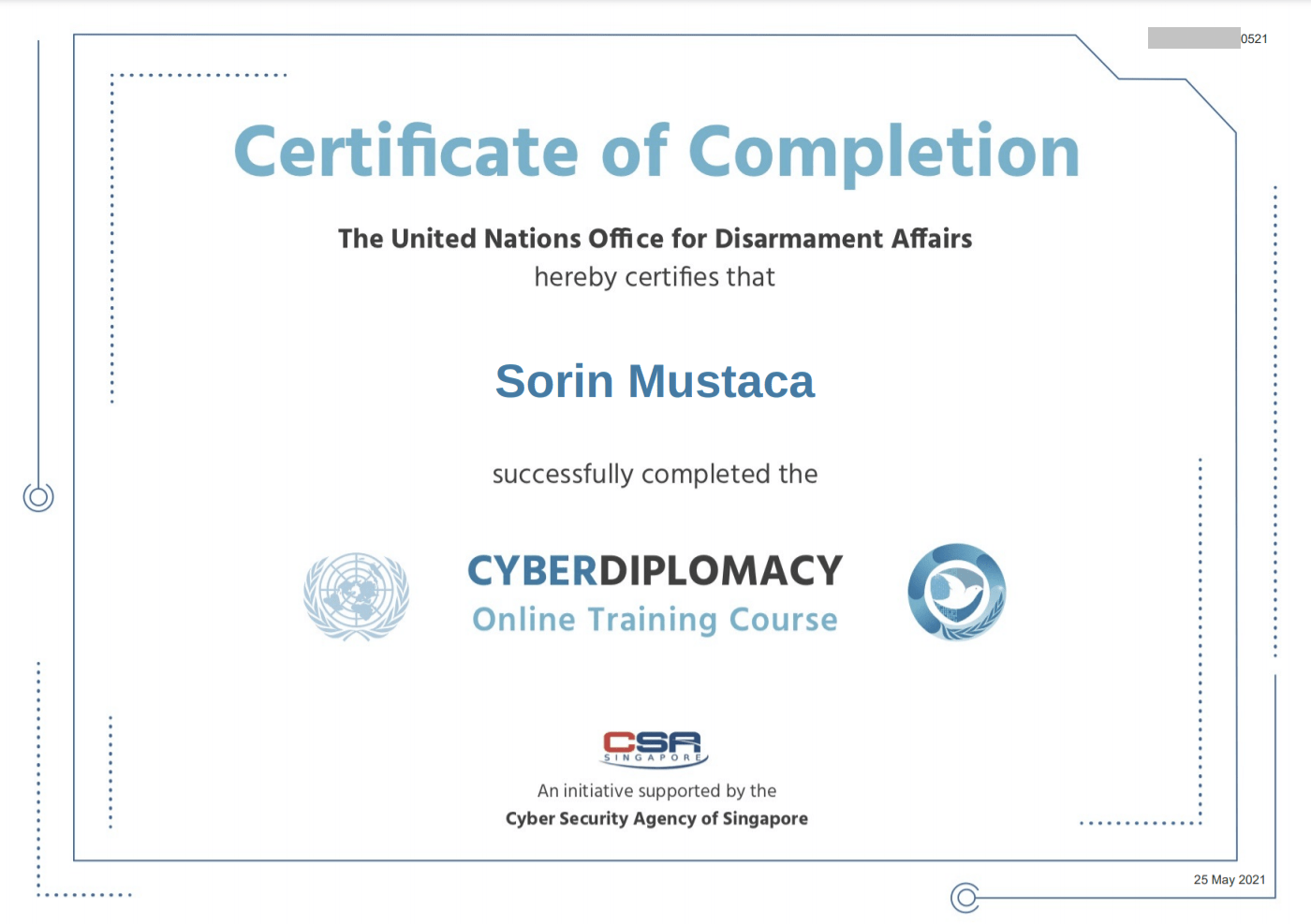
Cyber Diplomacy – a course from UN Office for Disarmament Affairs
I just finished the online course “Cyber Diplomacy“, a course from the United Nations Office for Disarmament Affairs. For me it was interesting to find out how much from the real world has been already applied to the cybersecurity world. Unfortunately, by seeing this, I realized that actually nobody cares about these UN resolutions. For […]
You must be logged in to post a comment.