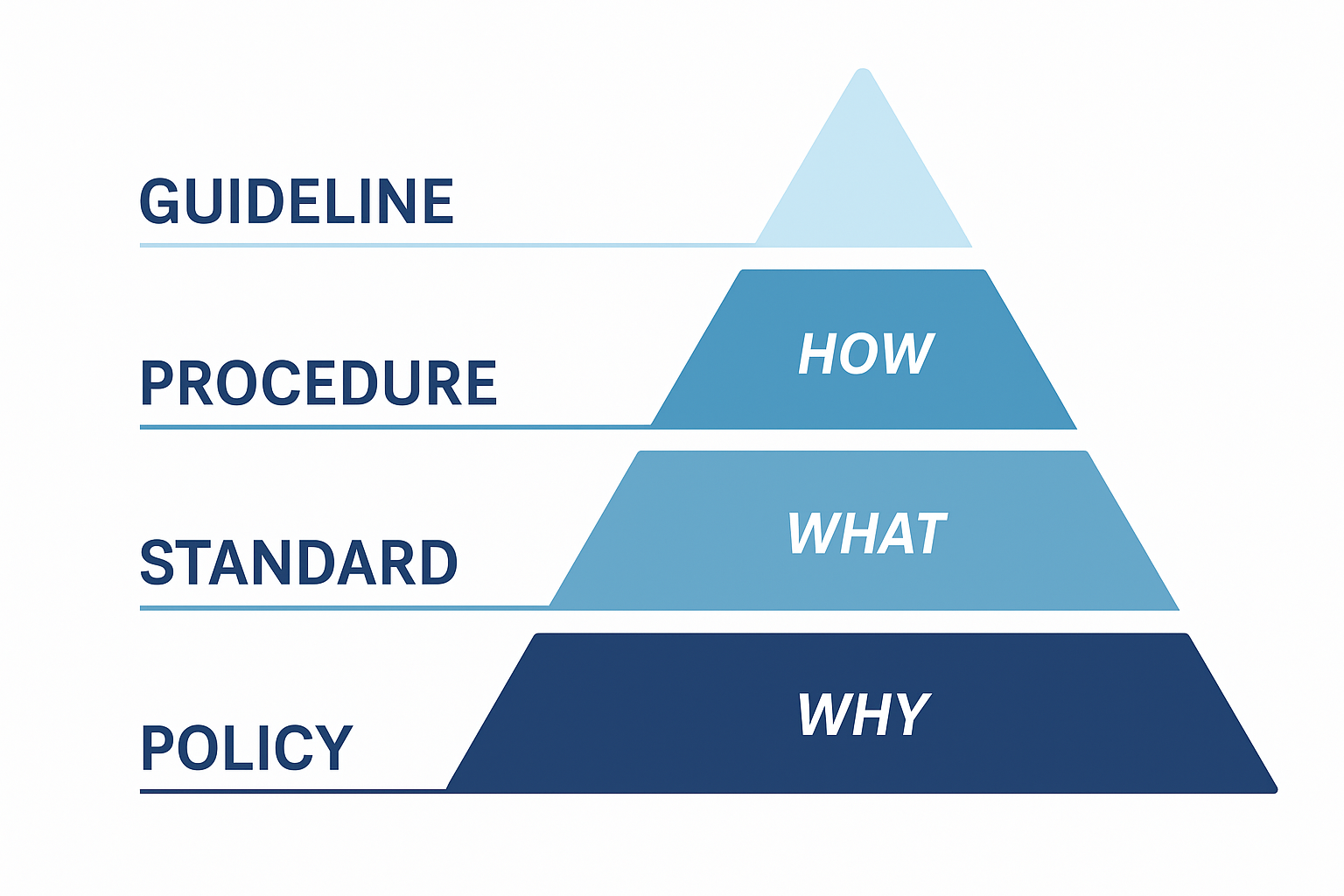
Policy vs Standard vs Procedure: why, what, how
Ever wondered what the differences between these terms are? We use them in GRC very often, but we rarely think what they mean. This creates in time some stretching of these concepts, meaning that their meanings overlap to a certain degree. A Policy is a high-level, mandatory statement of principles and intent. A Standard […]
You must be logged in to post a comment.