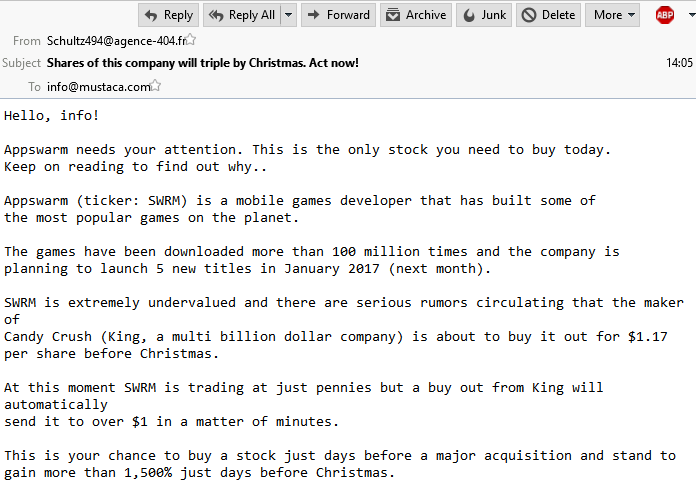
Stock spam is back!
After many years, the penny stock spam is back. Hello, info! <name> needs your attention. This is the only stock you need to buy today. Keep on reading to find out why.. <name>(ticker: <tick>) is a mobile games developer that has built some of the most popular games on the planet. The games have been […]









You must be logged in to post a comment.