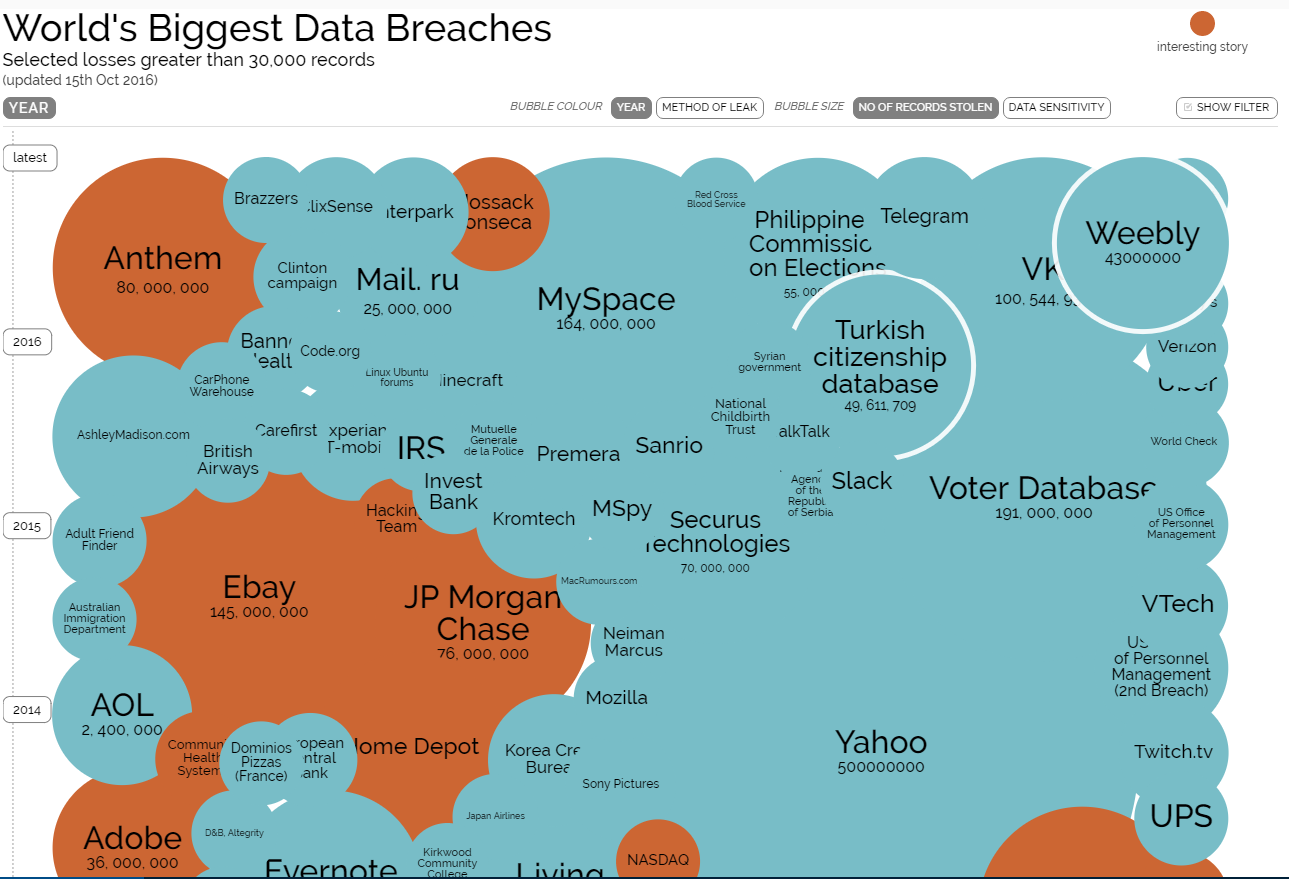
Scary to see details of the World’s Biggest Data Breaches
Source: http://www.informationisbeautiful.net/visualizations/worlds-biggest-data-breaches-hacks/ No worries, the chart is very interactive and you can select what you want to see by changing the filter: The problem is that if you select like the screenshot below, you will not see anything anymore. This is scary! Statistics? Actually, the data is scary: it seems that at any […]




You must be logged in to post a comment.