|
|
My company offers consulting on how to prepare for TISAX, ISO27001, NIS2, CSMS and SOC2 audits. |
|
||
| Get in touch with us here: https://www.endpoint-cybersecurity.com/contact/ |
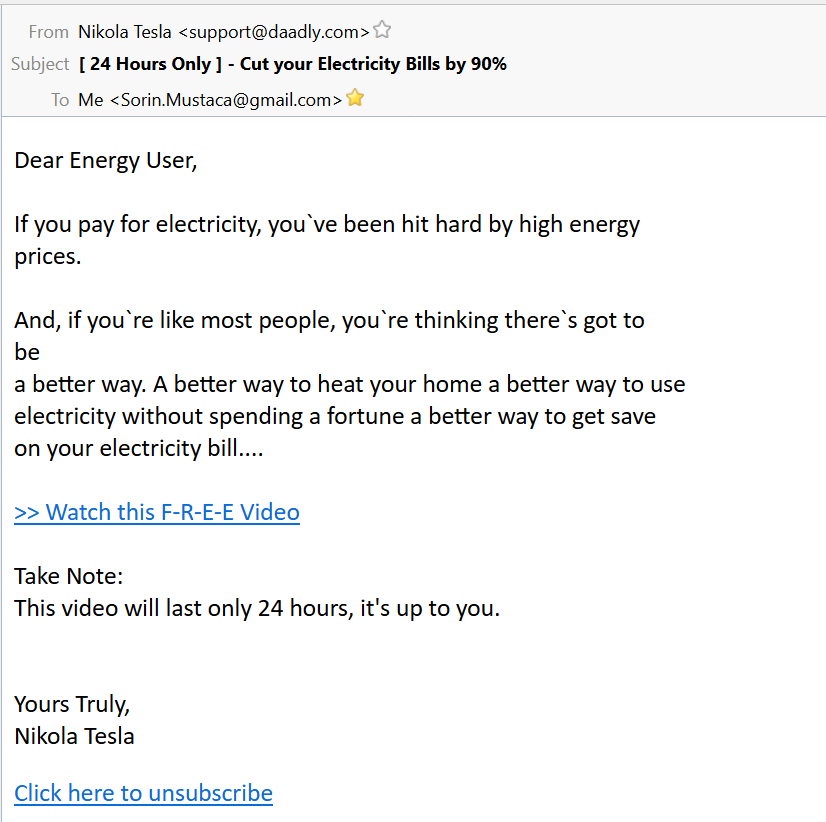
I wrote before about various tricks that cybercriminals use to attract people to do something (btw, this is called “social engineering”). This time, they make use of the well-known WhatsApp (written like I did and not like in the screenshot below) to redirect users to an online pharmacy website.
The funny thing is that the link behind the button “autoplay” goes to an IP address hosting a file with extension PL (coming from Perl) which means usually a script. The file contains just minimal JS code to redirect to the pharmacy page.
The email pretends to come from Whats App Reminder <billing@shapeupsf.org> which has nothing to do with WhatsApp. Of course, if you look in the headers, you see that the email address is spoofed.
What do we learn from here?
1. Always have a look at the sender and the recipient
2. Don’t ignore the small things like “WhatsApp” vs. “Whats App”. Usually the fraudsters don’t pay attention to details. You should.
3. Have a look where you click. The link behind the button should be inside the official domain (like whatsapp.com) and not to some strange server.
© Copyright 2014 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Want to work with me on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.

One thought on “Spam using WhatsApp voice mail”
Comments are closed.