Sign files unattended in batch mode while having an eToken (no password popup!) (updated)
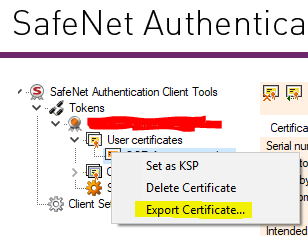
Expanding on answers already in this thread, it is possible to provide the token password using the standard signtool program from microsoft. 1. Export your public certificate to a file from the SafeNet Client 2. Find your private key container name 3. Find your reader name 4. Format it all together The eToken CSP […]