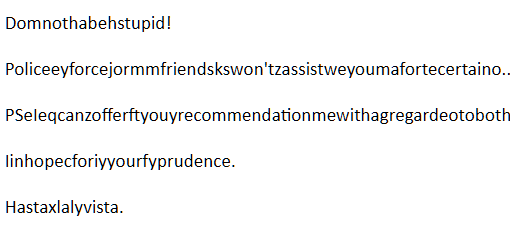
“Hastaxlalyvista” says a “hacker” who tries to blackmail me using an obfuscated mail
We’ve seen millions of emails with blackmailing texts containing some username/email address and a password harvested from some hacked website. This one would be just another one, except that the text is obfuscated 🙂 It looks interesting but it is tiresome to try to read it. And why the effort, in the end ? Below […]
You must be logged in to post a comment.