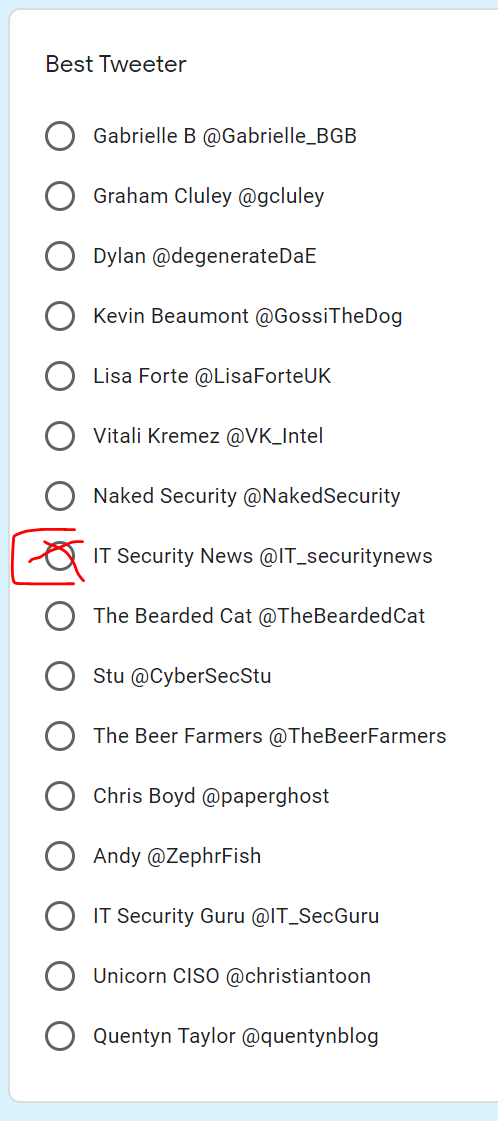
My IT_SecurityNews account nominated for “Best tweeter” account in the European Cybersecurity Blogger Awards
European Cybersecurity Blogger Awards – VOTE FOR YOUR WINNERS: Vote here . Yes, it is a Google Form… but there is no malware or spam 🙂 Don’t forget to vote IT_SecurityNews! The seventh annual European Cybersecurity Blogger Awards sponsored by Qualys and powered by Eskenzi PR, will be bestowed upon the best cybersecurity bloggers, podcasters, […]
You must be logged in to post a comment.