Dropbox phishing: someone is interested in your corporate files
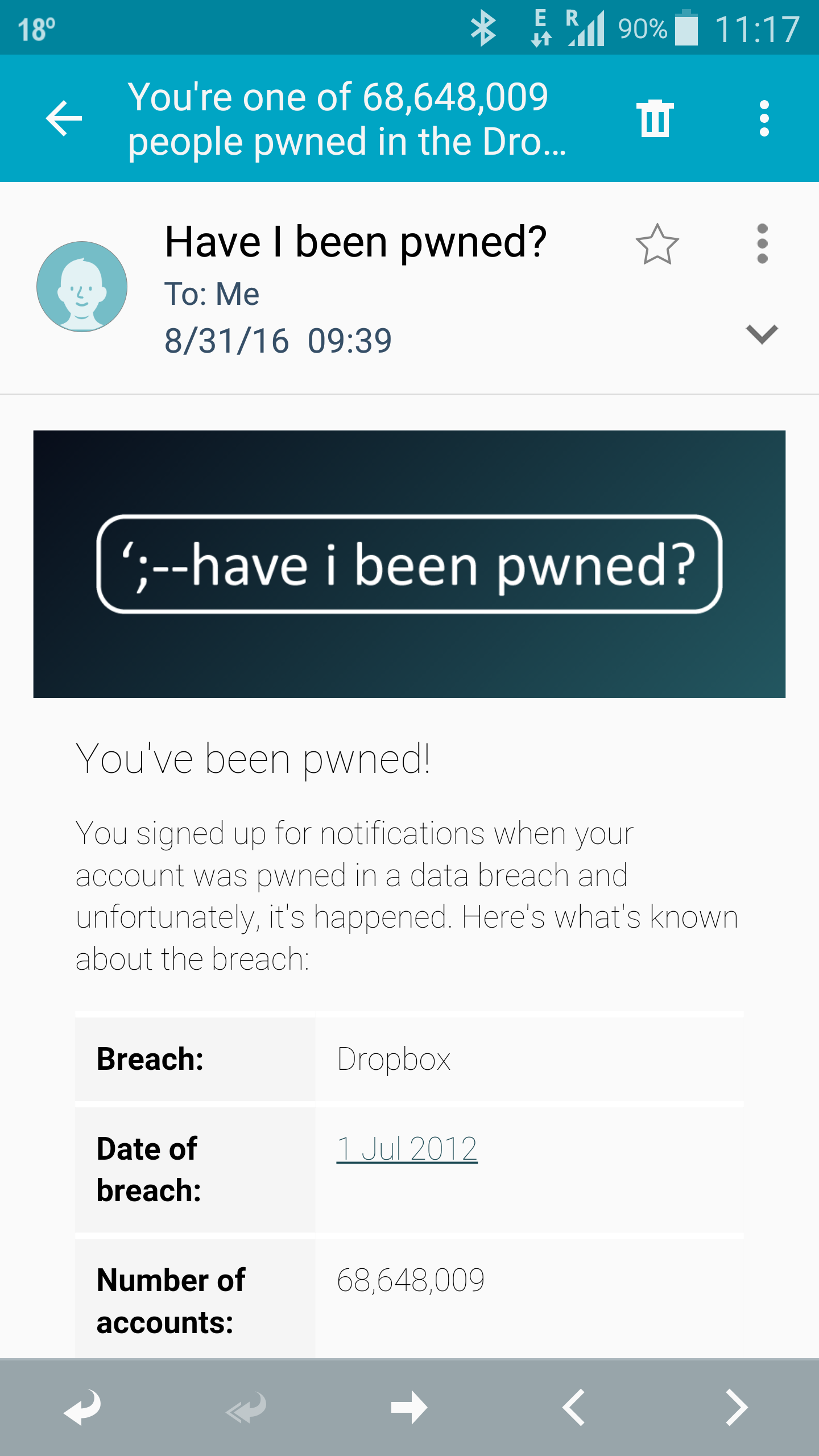
I wrote before about the Target Malware. Now I can also write about Phishing. Here is one for Dropbox: What is wrong with this email ? the contact me by extracting the user part in the email address (smustaca) The “Verify your email” goes directly to a phishing website. The text is rather […]

You must be logged in to post a comment.