Navigating AI Standards and Regulations
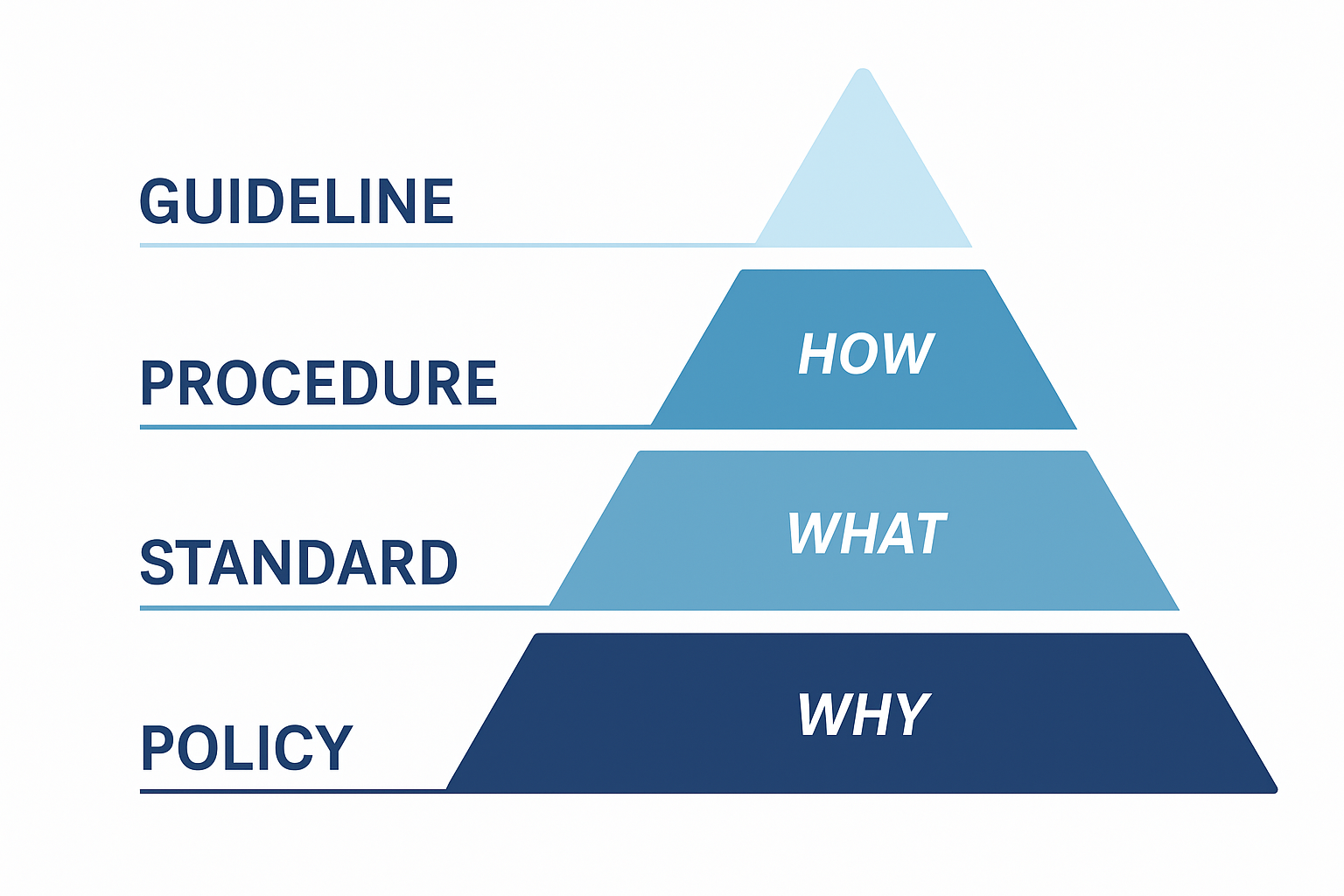
Note: This post is written with a lot of help from AI, used to summarize the standards mentioned below. Artificial intelligence (AI) is reshaping industries, but it also brings new risks. From security vulnerabilities to compliance challenges, organizations must balance innovation with responsibility. New standards were created and newer are emerging to guide this […]
You must be logged in to post a comment.