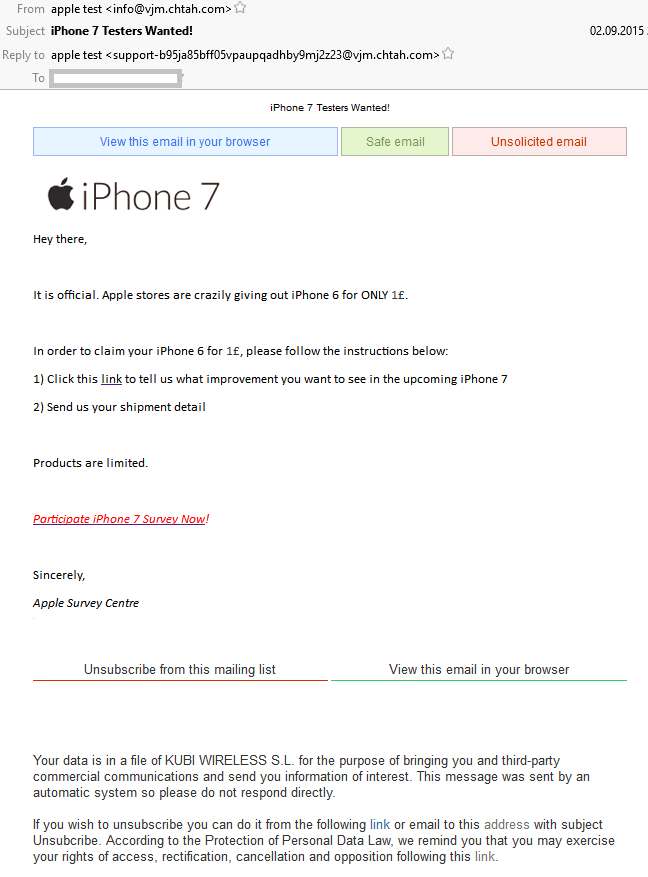
“Apple iPhone 7 testers wanted”: Probably the most complex scam I’ve seen this year!
This scam is sent by CHTAH.COM platform which is known to send millions of spam emails. You can see its added “value” by inserting the three colored rectangles on top of the mail. “iPhone 7 Testers Wanted!” is trying to lure the readers to a website that looks very much like the times.com website. […]
You must be logged in to post a comment.