Social engineering at its best: ransomware delivery methods
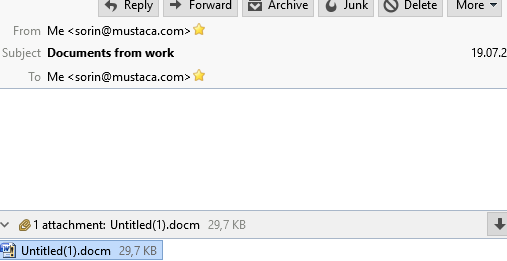
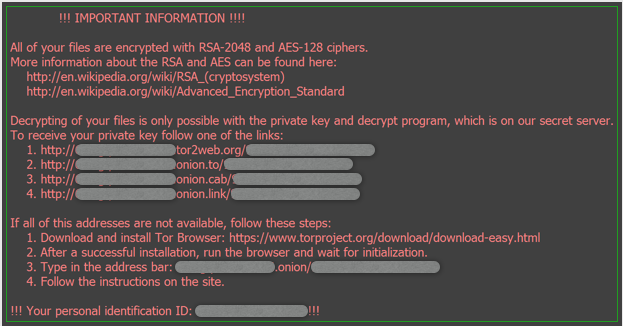
I wrote already about Ransomware (and here), but in a more generic way as I will do now. From me to me, with the subject “Documents from work” is the subject of a new Locky ransomware. Attached is a Word document containing macros. In the document (which is actually an archive) is a file called word\vbaProject.bin. […]
You must be logged in to post a comment.