I wrote already about Ransomware (and here), but in a more generic way as I will do now.
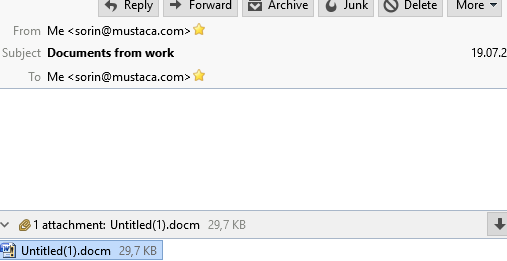
From me to me, with the subject “Documents from work” is the subject of a new Locky ransomware. Attached is a Word document containing macros.
In the document (which is actually an archive) is a file called word\vbaProject.bin. That file seems to be the trigger that downloads the ransomware binary.

This is the link to the VirusTotal detection: https://virustotal.com/en/file/28ba8362af69958964bf8d7e23664cddc625e67b55ff5d5e95e9feef74158e96/analysis/1469020147/
At the moment of writing this post, 30/53 engine detect it.
My goal is not to analyze here the ransomware, but the delivery.
The social engineering used here has as soly purpose to make the user to open and executed the attachment.
There are subjects of emails which simply “force” some people to open them without thinking.
- FW:Expenses Report # xxxx
- payment confirmation
- Additional Costs
- recent bill
- RE: Additional Information Needed #aaaaaa
What you MUST Do
The emails and attachments are not harmful just sitting in your inbox or Trash folder.
You MUST delete emails which you didn’t send and have these characteristics:
- from yourself to yourself
- contain attachments (archives, .JS, .DOC, .DOCX, .DOCM, XLS, .XLSX, etc.)
- have a blank body area or few lines of text
Have the rule delete the messages for you, so you don’t have to deal with them. Please remember that this is not a fool-proof way to deal with these messages. At any time the attackers may change their tactics, invalidating these rules.
You SHOULD NOT extract the attachment or open the extracted file.
© Copyright 2016 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Interested in professional consulting on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.
You must be logged in to post a comment.