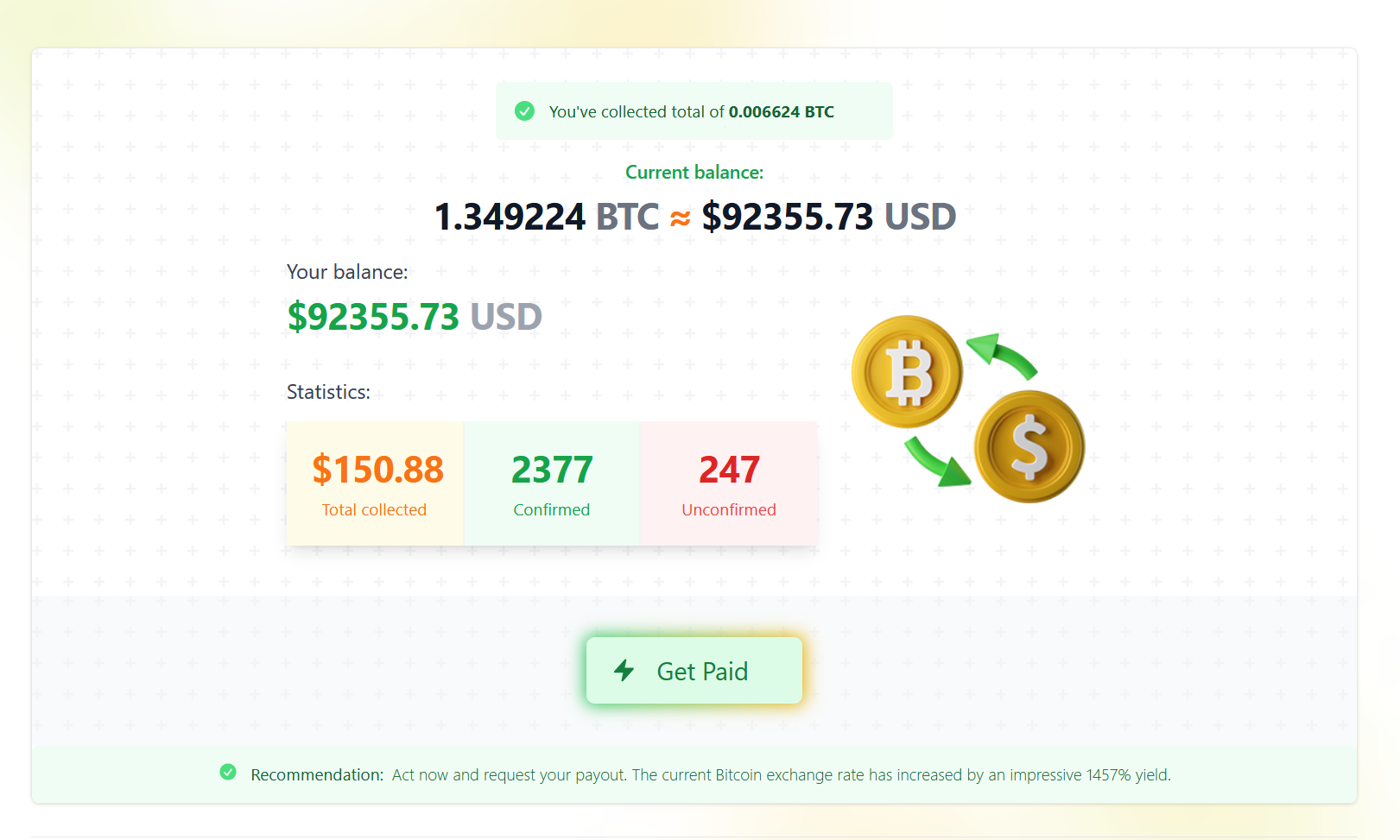
Bitcoin fraud through (hacked?) WordPress installations
I don’t usually write anymore about phishing attempts, but this one draw my attention due to large amount of emails and to variety of websites being used. Of course, I would not write “massive” if I would have received 1-10, but I receive about 10 a day. Fortunately, almost all go to Spam folder. Gmail […]
You must be logged in to post a comment.