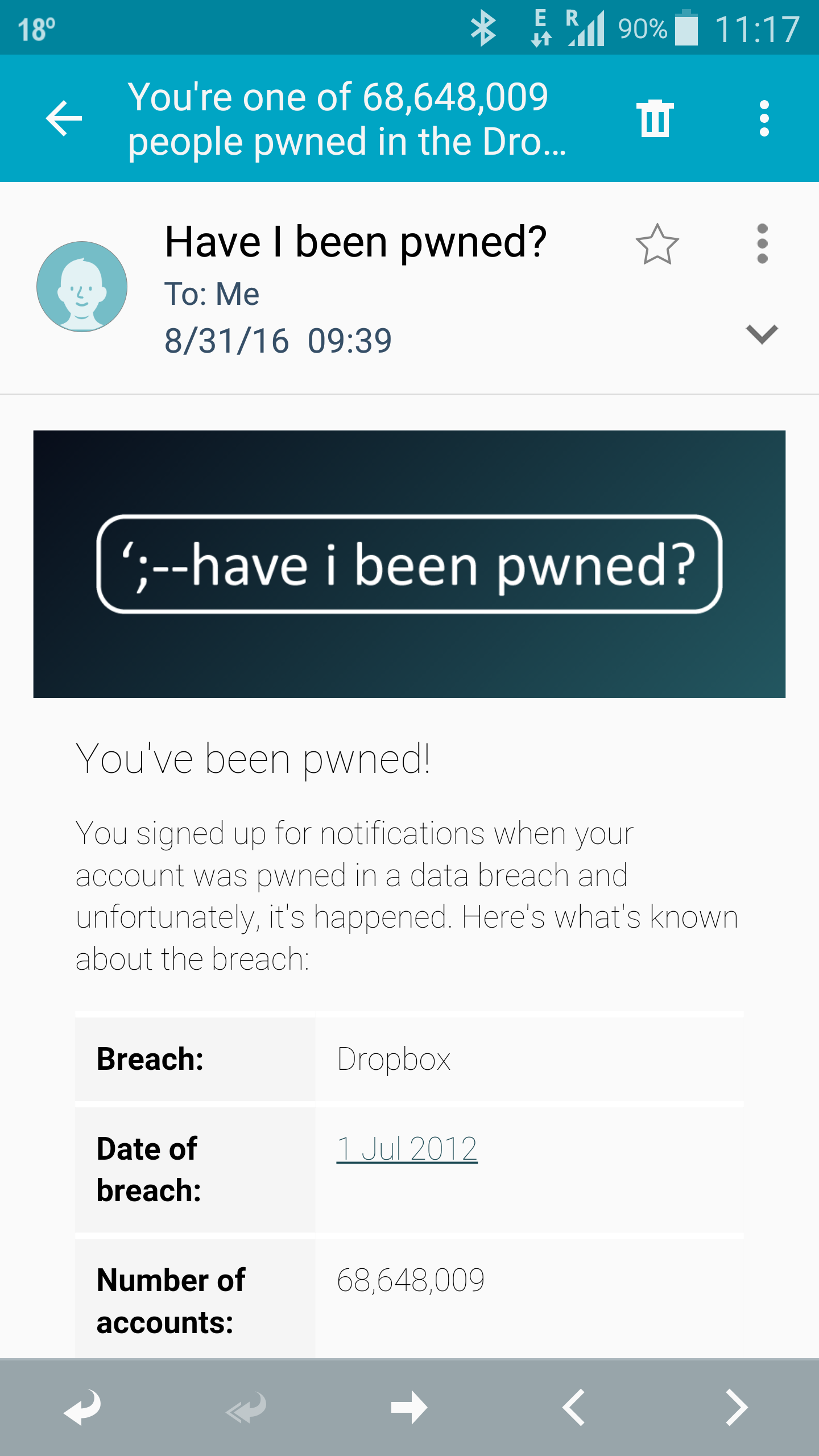
Dropbox was breached in 2012, the data is now online – a quote in SecurityWeek
68 Million Exposed in Old Dropbox Hack By Ionut Arghire on August 31, 2016 In an email response to a SecurityWeek inquiry, IT security expert Sorin Mustaca said that the surprising fact is that the 2012 hack of Dropbox didn’t emerge earlier, along with the other mega-breaches. He also notes that the use of the […]
You must be logged in to post a comment.