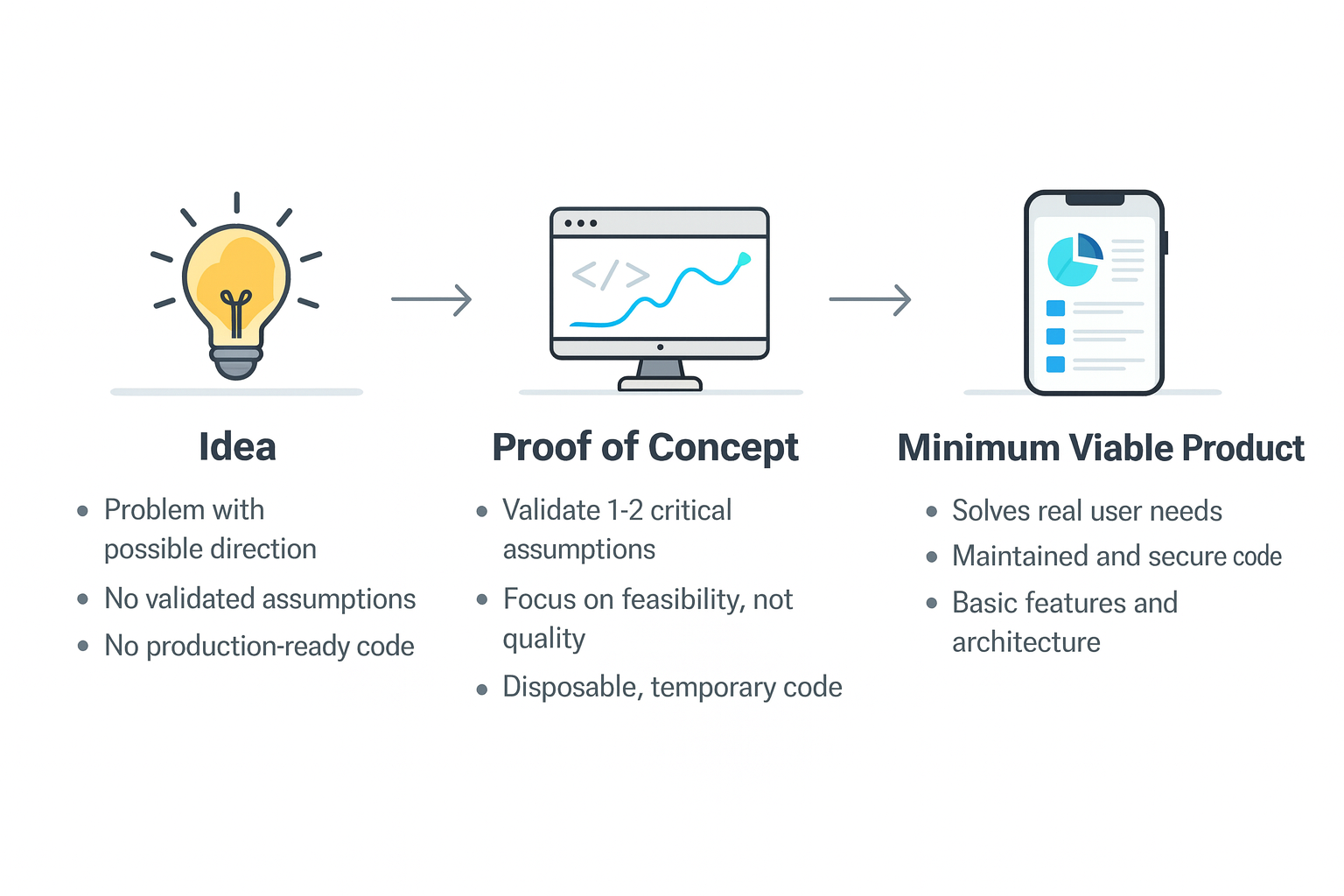
From Idea to Proof of Concept to MVP – 3 article series
This is a a developer focused guide in three parts to evolving code, architecture, and processes with the purpose of turning a raw concept into a usable product. This process is one of the hardest parts of software development. Teams often jump into implementation too early, or they build something polished before testing whether the […]