IT Security News has its own Android App
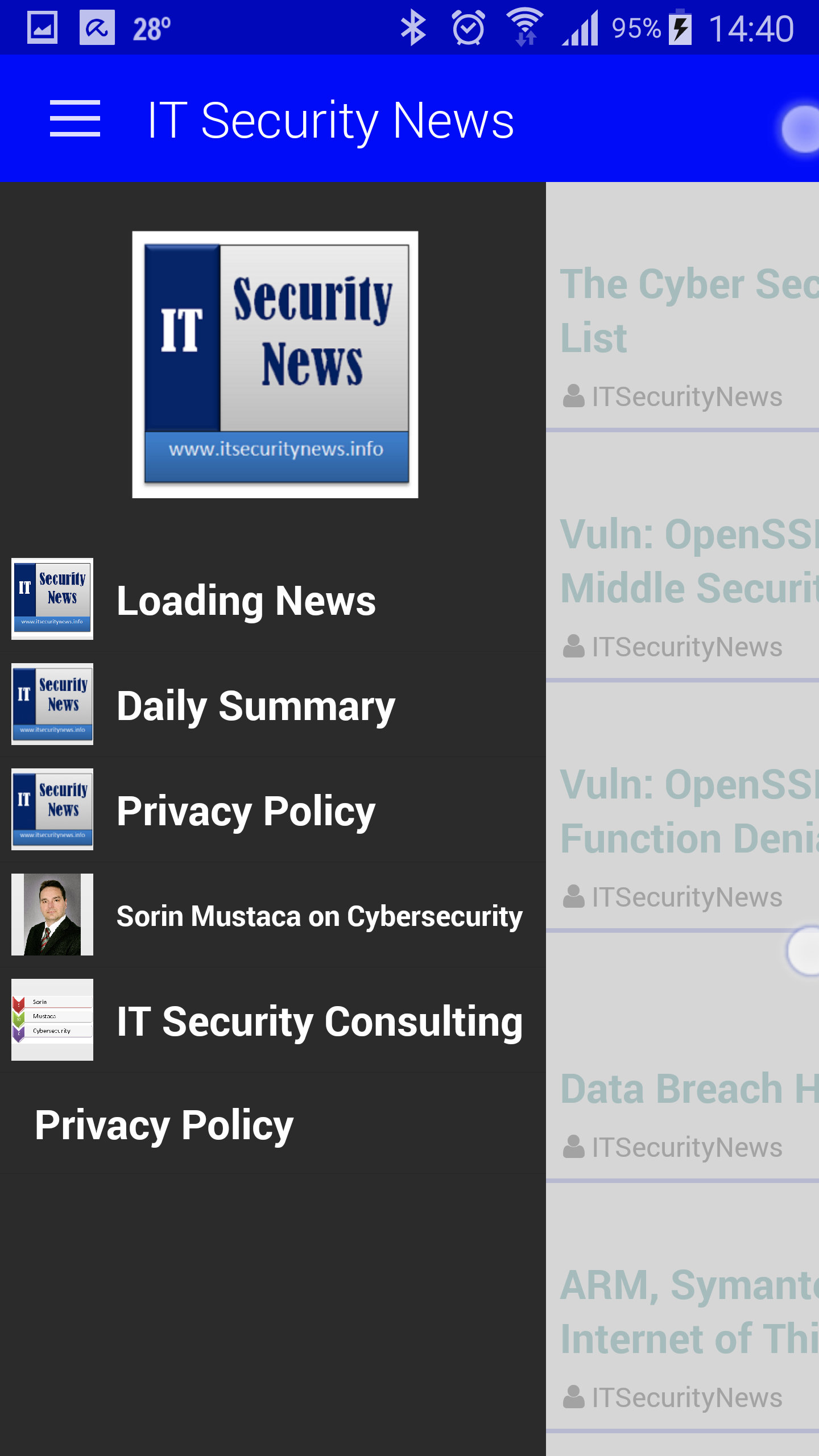
I have finally found the time to make the app I always wanted to have for the “IT Security News” service. Here is the page on Google’s Play Store: And the screenshots of the app: Right now it is available only on Android devices, soon it will be available in the […]
You must be logged in to post a comment.