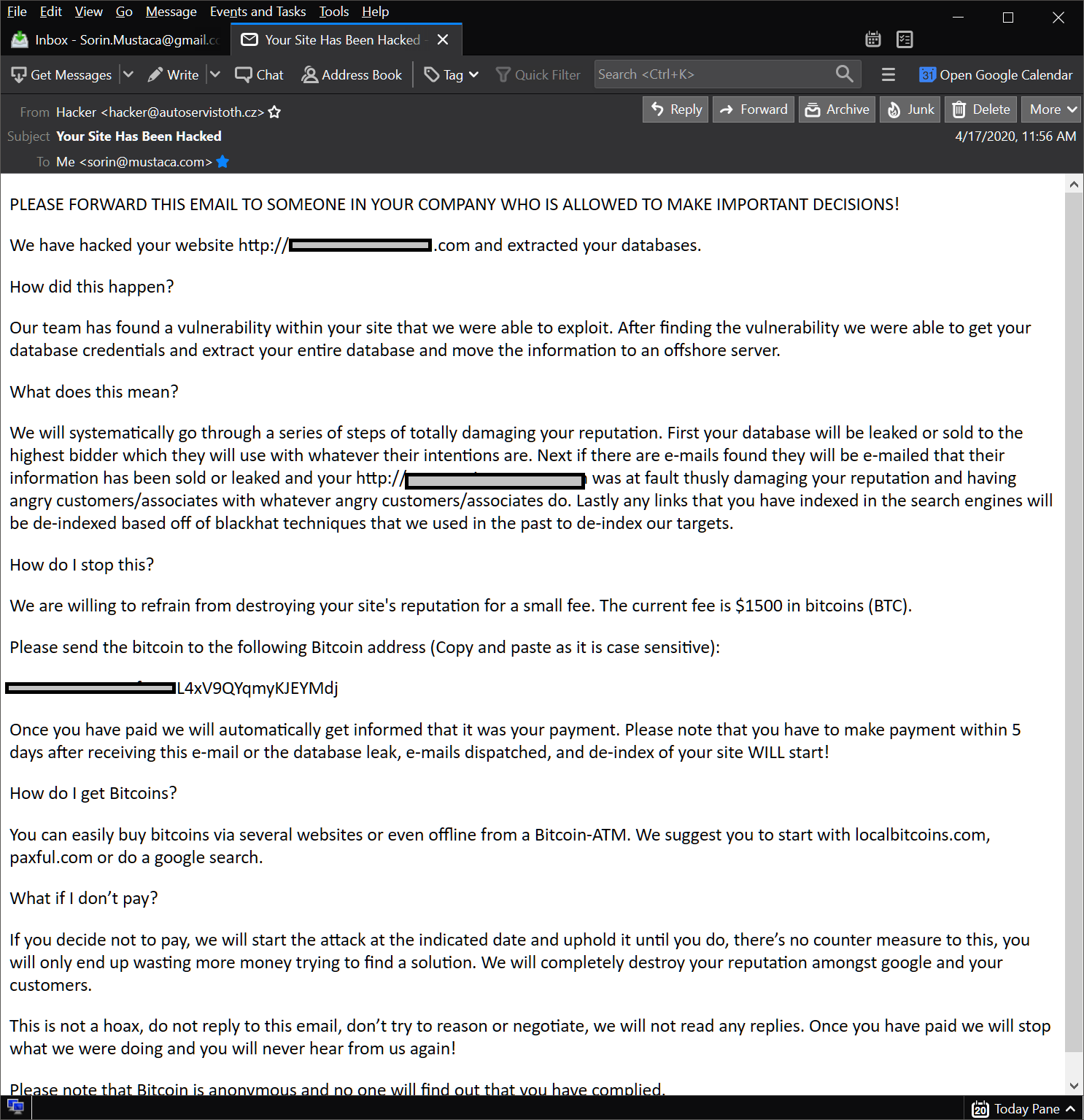
“Your Site Has Been Hacked” ransomware email campaign in the wild
I was actually not expecting this kind of ransomware… I am used by now with “You’re hacked”, “You’re infected”… and others alike , but this one with the website is actually really interesting. What I find very disturbing is the fact that there are 5 transactions. A few were for tests, I think, but there […]
You must be logged in to post a comment.