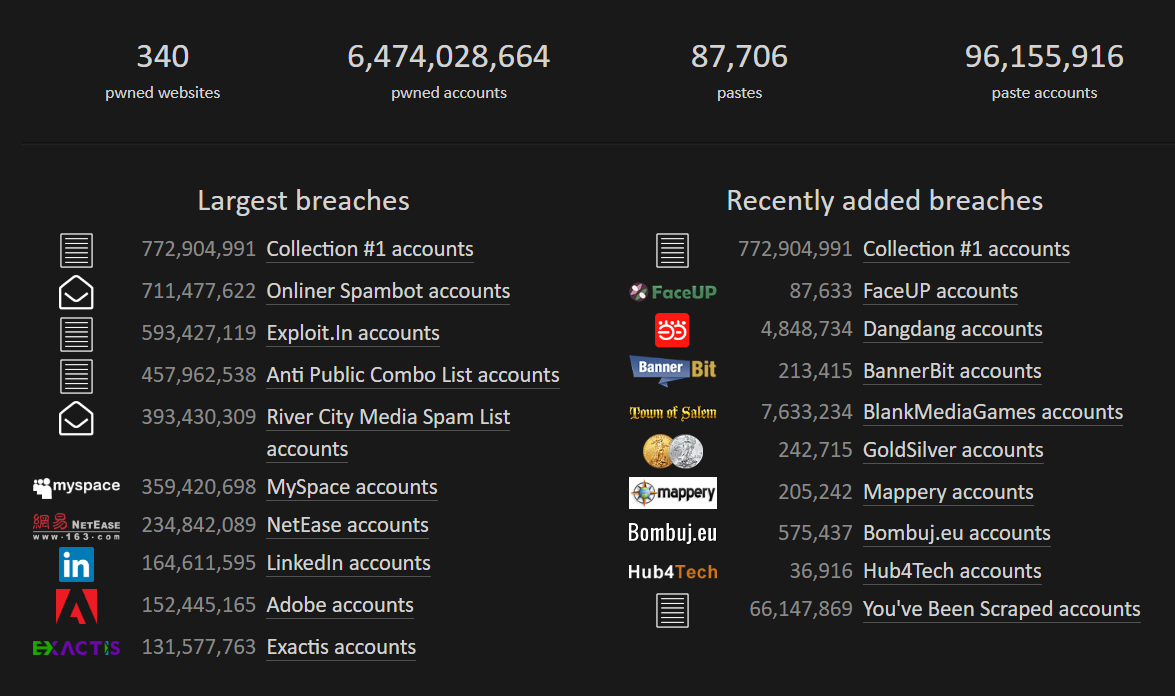
Every week I hear about a new breach that lost millions or billions of accounts and “somebody” publishes them online.
Do not forget to register at https://haveibeenpwned.com/ for real-time notification in case your email appeares somewhere online.
|
|
My company offers consulting on how to prepare for TISAX, ISO27001, NIS2, CSMS and SOC2 audits. |
|
||
| Get in touch with us here: https://www.endpoint-cybersecurity.com/contact/ |

Here is a new case of Sextorsion – it gets more technical this time.
This is another very good attempt to extort money from unsuspecting and unware people who had their email address and password on some website, which got hacked.
We wrote before about sextorsion, even using an old real password of the respective account.
However, the fraudsters have taken the extorsion email to a whole new level now.
If before the discussion as about some “software” which was downloaded from suspicious websites the receiver of the email visited, now we are talking more seriously.
The “spyware software developer” contacted us because he allegedly hacked the Cisco router used to connect to the Internet. There is even a CVE number of the vulnerability: CVE-2018-0296.
Now, this might sound very realistic, but even if you would have some knowledge about routers and their security, it is enough just to read the Summary of the exploit:
A vulnerability in the web interface of the Cisco Adaptive Security Appliance (ASA) could allow an unauthenticated, remote attacker to cause an affected device to reload unexpectedly, resulting in a denial of service (DoS) condition. It is also possible on certain software releases that the ASA will not reload, but an attacker could view sensitive system information without authentication by using directory traversal techniques.
It says that one enterprise appliance is vulnerable due to a software bug, which could lead to a DOS or, for some versions, to exposure of sensitive information. By no mean it is possible to send some malware to a system behind this appliance!
Now, that we clarified this, we hope it is clearer that the email is just a bad joke, meant to scary people.
Here is the text of the email:
Dear user of gmail.com!
I am a spyware software developer.
Your account has been hacked by me in the summer of 2018.
I understand that it is hard to believe, but here is my evidence:
– I sent you this email from your account.
– Password from account <your email>: <some random text> (on moment of hack).
The hacking was carried out using a hardware vulnerability through which you went online (Cisco router, vulnerability CVE-2018-0296).
I went around the security system in the router, installed an exploit there.
When you went online, my exploit downloaded my malicious code (rootkit) to your device.
This is driver software, I constantly updated it, so your antivirus is silent all time.
Since then I have been following you (I can connect to your device via the VNC protocol).
That is, I can see absolutely everything that you do, view and download your files and any data to yourself.
I also have access to the camera on your device, and I periodically take photos and videos with you.
At the moment, I have harvested a solid dirt… on you…
I saved all your email and chats from your messangers. I also saved the entire history of the sites you visit.
I note that it is useless to change the passwords. My malware update passwords from your accounts every times.
I know what you like hard funs (adult sites).
Oh, yes .. I’m know your secret life, which you are hiding from everyone.
Oh my God, what are your like… I saw THIS … Oh, you dirty naughty person …
I took photos and videos of your most passionate funs with adult content, and synchronized them in real time with the image of your camera.
Believe it turned out very high quality!
So, to the business!
I’m sure you don’t want to show these files and visiting history to all your contacts.
Transfer $823 to my Bitcoin cryptocurrency wallet: 1ARbihuSkEAojNHgxsgFVKjTJDHXuimB8
Just copy and paste the wallet number when transferring.
If you do not know how to do this – ask Google.
My system automatically recognizes the translation.
As soon as the specified amount is received, all your data will be destroyed from my server, and the rootkit will be automatically removed from your system.
Do not worry, I really will delete everything, since I am ‘working’ with many people who have fallen into your position.
You will only have to inform your provider about the vulnerabilities in the router so that other hackers will not use it.
Since opening this letter you have 48 hours.
If funds not will be received, after the specified time has elapsed, the disk of your device will be formatted, and from my server will automatically send email and sms to all your contacts with compromising material.
I advise you to remain prudent and not engage in nonsense (all files on my server).
Good luck!
A rather long email, meant to touch as many points as possible for a large audience.
How to recognize these scams
1. The email is sent by your email address to you.
2. It is addressed in a common style, without any idea of who you are.
3. It talks about technical terms, in order to impress and convince the audience. However, it has no substance.
4. It uses words which appear to come from an automatic translation software.
5. It requests payment in bitcoins in order to remain fully anonymous.
6. It threatens to notify your contacts of your online activities.
© Copyright 2019 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Interested in professional consulting on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.

You must be logged in to post a comment.