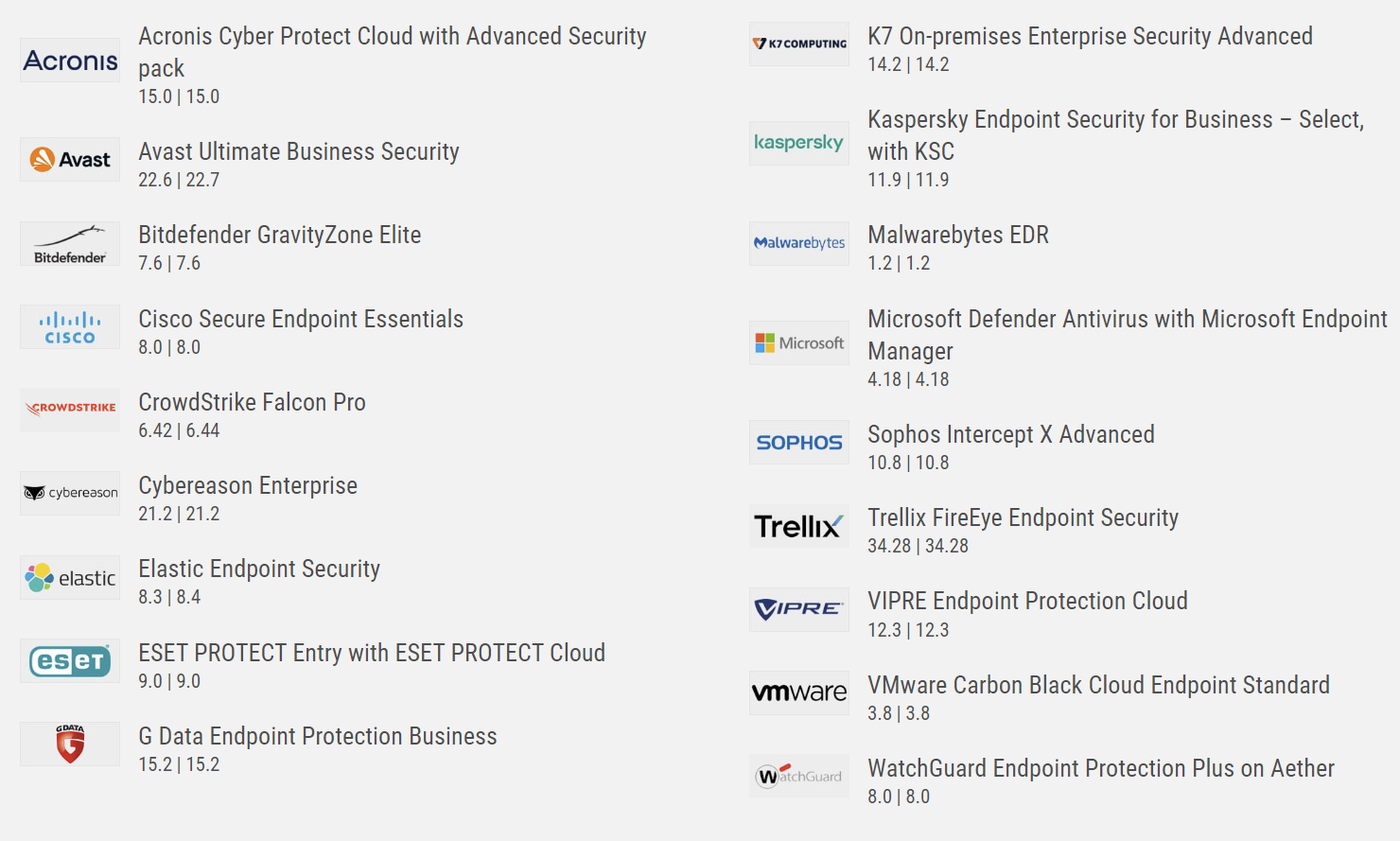
Av-Comparatives did a long-term test of security Business Products. The details can be seen here: https://www.av-comparatives.org/tests/business-security-test-august-september-2022-factsheet/
Initially, I wanted to write about this test because I was surprised to see how well Microsoft Defender performed.
But then, I started to read the details, even if the full report will only be released in December 2022.
Read below the things which surprised me:
- Engines used
Information about additional third-party engines/signatures used by some of the products:
Acronis, Cisco, Cybereason, G Data, Trellix and VIPRE use the Bitdefender engine (in addition to their own protection features).
VMware uses the Avira engine (in addition to their own protection features).
G Data’s OutbreakShield is based on Cyren.
Of course, most of this is not new …
What surprised me was:
- Cisco is using Bitdefender
- Watch Guard, Crowdstrike and K7 have own engines
- Crowdstrike’s ML engine is good
- G Data is using also Cyren
2) The special settings are not even close to the defaults.
It is normal that in business environments, and with business products in general, to be configured by the system administrator, in accordance with vendor’s guidelines and their own expectations.
But, this also tells me that there can be huge differences in the detection, performance and FP rate of the same product, depending on how it was configured.
I don’t find this good because I don’t know any administrator who reads manuals of security products. Also, they admins contact vendors’ technical support usually only after it is too late and the damage has occurred already.
So, if two persons would be testing the same product, with the same samples, but would configure the product differently (not necessarily wrong, just differently) they would get a different detection rate and a different performance.
3) Engine vs. FP rate
It can be seen in the tables that companies using the same engine (e.g. Bitdefender’s) have quite different results.
This is an effect caused by several factors:
a) configuration of the engine – this is the smallest effect in my opinion, because the fine-tuning of the detection is made in the application and less in the engine
b) own detection features of the end product
c) cloud services used, which are not visible in the comparison
d) 3rd parties detection mechanisms, added at low level (driver, service) or in the end-product
4) I have missed several “classical” enterprise products
- F-Secure – using Avira’s engine and their own detection and cloud services
- McAfee
- Symantec
- Norton Lifelock – probably still using Symantec engine and not yet Avast or Avira
- TrendMicro
Conclusion
As I wrote at the beginning, I started writing this article because of Microsoft Defender.
The product (with different names) has been around since ~2004, after Microsoft bought RAV Antivirus, where I used to work.
For many years it has been advertised by Microsoft as the absolute minimum security product on a Windows PC.
However, in the past 3-4 years the product has been significantly improved, the detection rate has sky-rocketed and the FP was reduced to almost zero.
No wonder that many consumers ask why would they pay for a security product when Defender is already doing a great job. And they are right !
I also know that small to large enterprises are using Defender to protect their computers, although it is fair to say that they also take a multi-layered defense approach.
So , I am worried that the AV industry is being slowly but surely pushed with the back to the wall by Defender.
But I know that the people working in the industry know this and they have started to find new and innovative ideas to protect their users’ computers.
© Copyright 2022 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Interested in professional consulting on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.