German users are receiving a lot of such spams these days:
It is about a package which allegedly it has its transport costs not paid. (2 €).
The user is invited to visit a page where he can be pay this.
|
Useless to say, this is not the usual way to deal with packages, so those which sent the spam have no idea how things work.
The link goes to a page delivering a malicious payload.
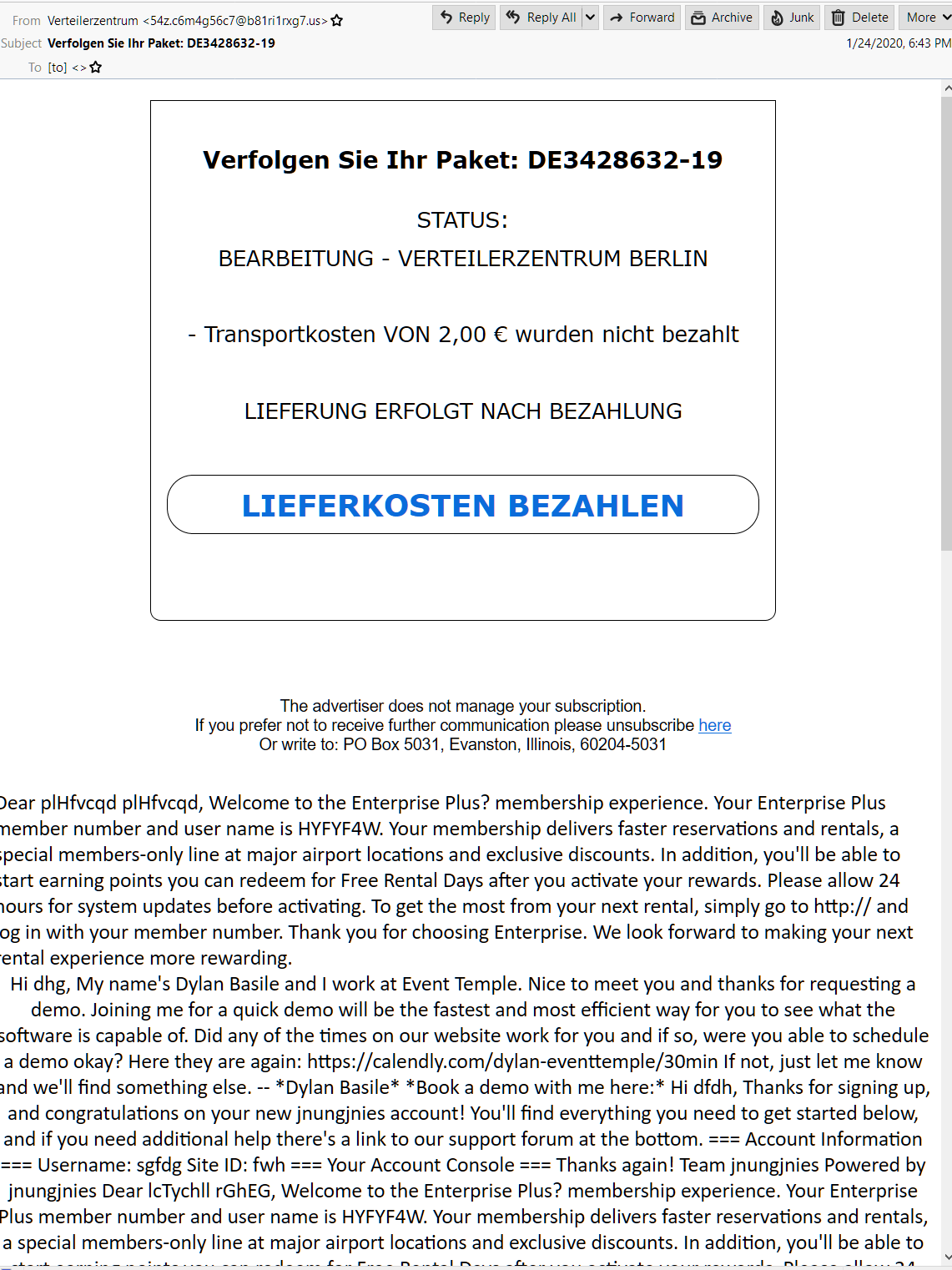
This is how the email looks like:

Observe the blue marked items.
The spammers are either lacking skills, or they think that the users are idiots, or are themselves idiots.
The body of the email is one single line of Base64 encoded text.
It appears to be sent from an AWS account.
Received: from domain.com (ec2-52-193-124-80.us-west-1.compute.amazonaws.com [35.181.165.41])
by mx.google.com with ESMTP id d8si40042704pgv.61.2019.07.23.01.00.43
for ; Fri, 24 Jan 2020 12:43:25 -0500 (EST)
Received: from smtp.J51G83V9.org (enr2-mrelay-01.ad4123fb38497b9631680eea23dbd0b2.org. ) by mx.google.com with ESMTP id t6si5997511qvm.25.2019.02.12.06.38.06 for ; Fri, 24 Jan 2020 12:43:25 -0500 (EST)
Received: from pdr8-services-05v.prod.J51G83V9.org (HELO pdr8-services-05v) () by smtp.J51G83V9.org with SMTP; Fri, 24 Jan 2020 12:43:25 -0500 (EST)
Received: from pdr8-services-05v.prod.J51G83V9.org (ip6-localhost ) by pdr8-services-05v (Postfix) with ESMTP id J51G83V9 for ; Fri, 24 Jan 2020 12:43:25 -0500 (EST)
Date: Fri, 24 Jan 2020 12:43:25 -0500 (EST)
From: =?UTF-8?B?VmVydGVpbGVyemVudHJ1bQ==?= <54z.c6m4g56c7@b81ri1rxg7.us>
To:[to]
Message-ID: <tp1w50agsp.tp1w50agsp.tp1w50agsp.javamail.tomcat@pdr8-services-05v.prod.j51g83v9.org>
Subject: =?UTF-8?B?VmVyZm9sZ2VuIFNpZSBJaHIgUGFrZXQ6IERFMzQyODYzMi0xOQ==?=
MIME-Version: 1.0
Content-Type: text/html; charset=utf-8
Content-Transfer-Encoding: base64
PCFkb2N0eXBlIGh0bWw+DQo8aHRtbD4NCjxoZWFkPg0KPG1ldGEgaHR0cC1lc.....
This is the link analysis from VirusTotal: https://www.virustotal.com/gui/url/5578a666a2cb82c9e008ab6882324441a9d1a40d4ef1206e1ac9517e2efdabcf/detection
5 from 72 engines were detecting it at the time of writing this post.
You must be logged in to post a comment.