The importance of user names in WordPress
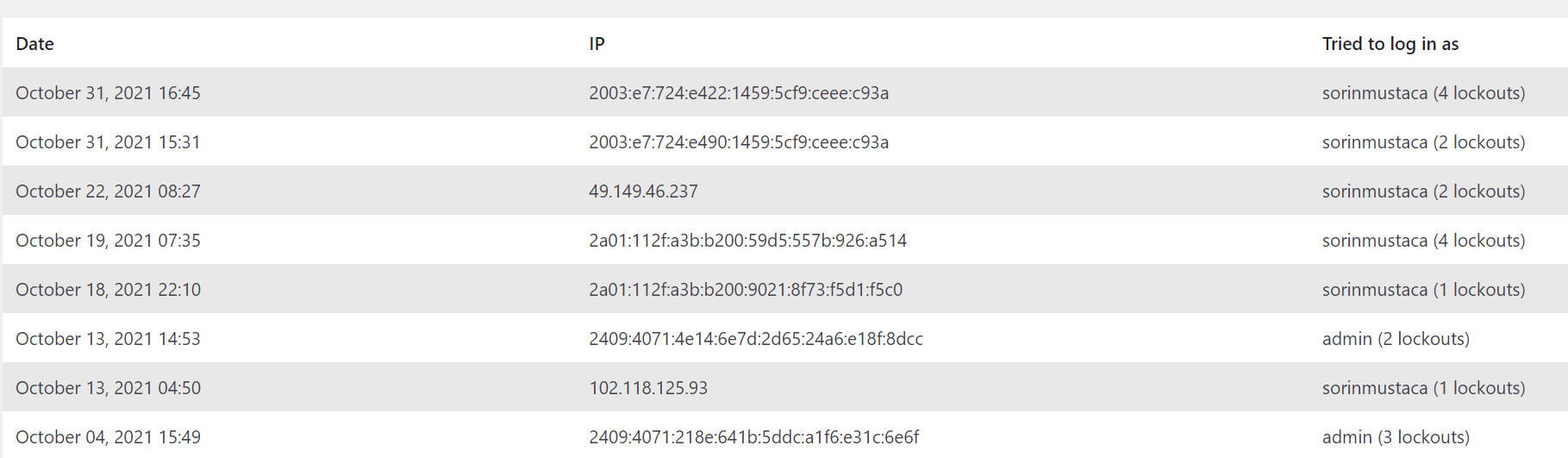
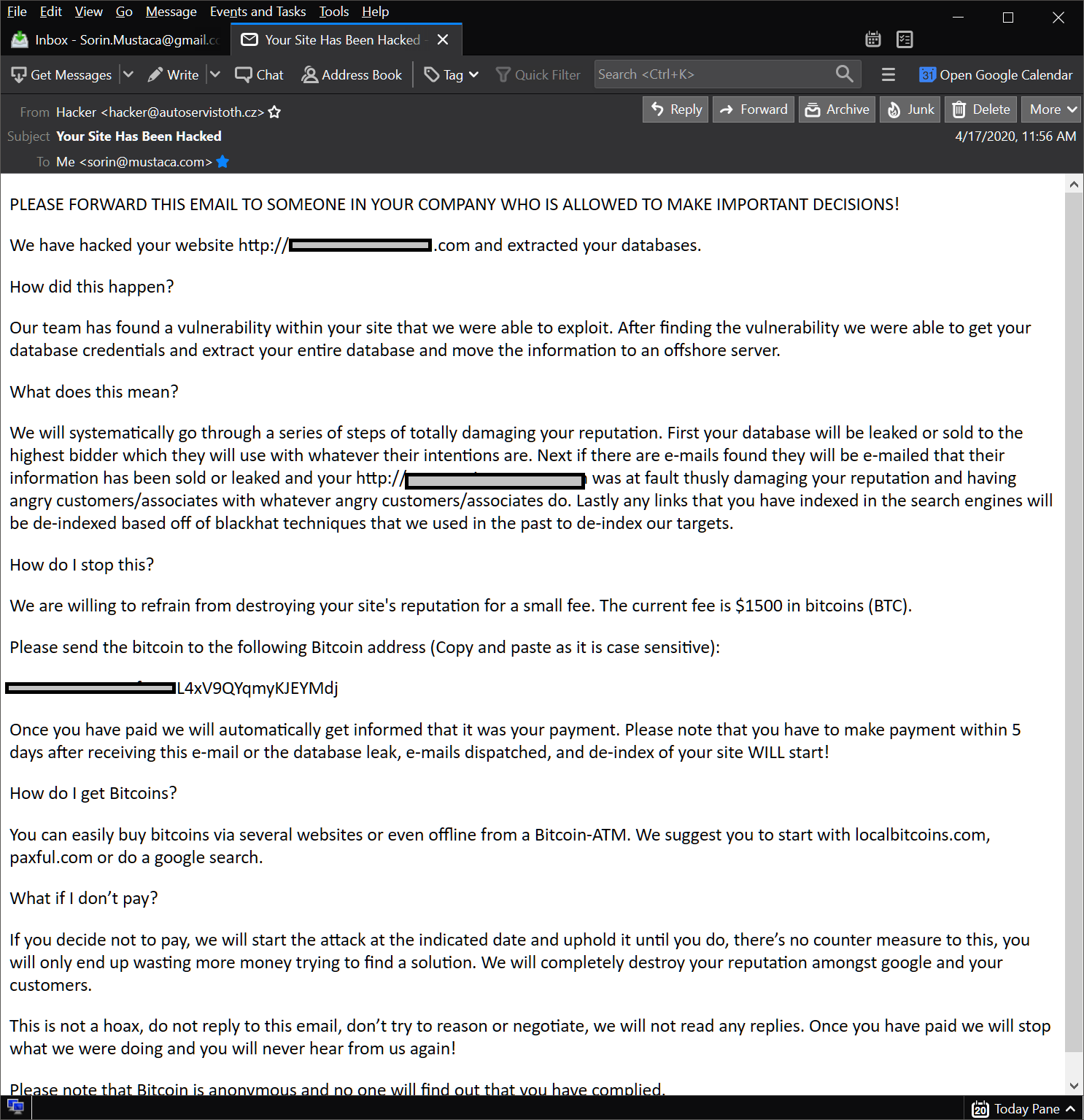
I have a plugin that prevents multiple unsuccessful logins. As can be seen, the spammers try several combinations like: admin (the default), then site name, and several others. It is critical to create a user name that is different than the obvious names, especially the default username “admin”. Another interesting thing is that I get […]


You must be logged in to post a comment.