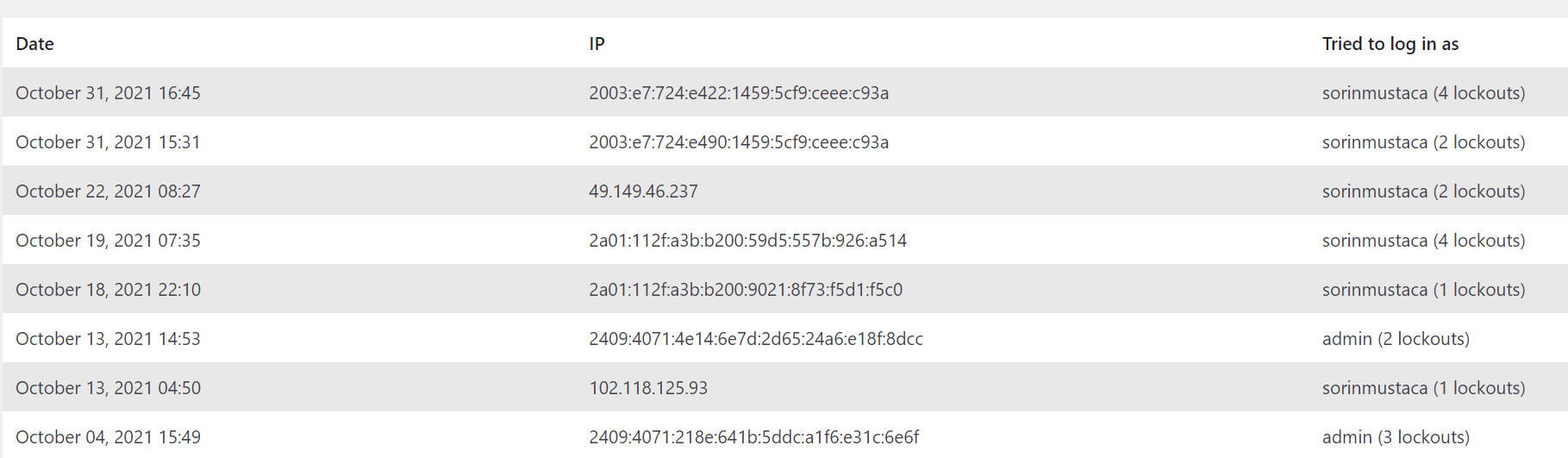
I have a plugin that prevents multiple unsuccessful logins.
As can be seen, the spammers try several combinations like: admin (the default), then site name, and several others.
It is critical to create a user name that is different than the obvious names, especially the default username “admin”.
Another interesting thing is that I get both IPv4 as well as IPv6 IP addresses. More and more IPv6.
Also, a spammer will continuously try to hack you, because they have automated scripts.
So, it makes sense to block them for a longer time.

For example, I use these settings:

The plugin I am using is “Limit Login Attempts Reloaded”.
I am not affiliated with them in any way.
© Copyright 2021 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Interested in professional consulting on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.
You must be logged in to post a comment.