Source: http://www.securityweek.com/45-million-potentially-impacted-verticalscope-hack
Author: Ionut Arghire, Security Week
Here is my longer comment:
LeakedSource writes on their website about a massive breach of VerticalScope.com and all its affiliated websites from February 2016.
However, neither VerticalScope.com nor any of the websites mentioned in the LeakedSource page mention anything related to a hack.
Even if denial of a breach is not something unseen before, after reading the Summary of the dump on LeakedSource I am starting to see here a pattern: “Each record may contain an email address, a username, an IP address, one password and in some cases a second password”. This is exactly the same as in the Myspace breach:”Each record may contain an email address, a username, one password and in some cases a second password.”
How come that two completely unrelated breaches share the dump format? Could it be that they are converted somehow into a single format before they are put on sale?
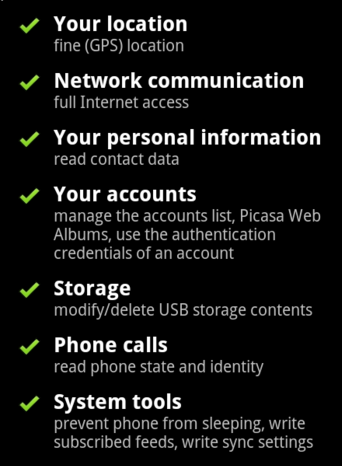
The assumption regarding the VerticalScope hack is that they used some vulnerable vBulletin software. I have verified this myself and this is why I found on a couple of their websites:

Doing a search on “vulnerabilities for vBulletin 3.8.7 Patch Level 3” can find on the first page various hacking tools. I haven’t tested any myself, but from their description they vary from cracking the licensing protection of vbulletin.com to sending spam and dumping data.
Some other very well known websites belonging to the VerticalScope group are WordPress instances. Those that I tested were running WordPress 4.2.4 (released on August 4, 2015). The latest version of WordPress is latest one is 4.5.2. Some plugins that are visible in these WordPress instances are also pretty outdated as well. We can’t exclude the fact that some of the plugins they use (Yoast SEO, NextGen Gallery, Better Related) might contains some vulnerabilities that hackers can easily exploit. WordPress runs a complete transparency policy for their software and for the plugins and themes used in WordPress.
What is disturbing for me to see is that VerticalScope writes on their blog that they will enhance the security of the passwords stored and they don’t even mention anything related to updating their potentially vulnerable software.
Seeing this mix of WordPress and VBulletin makes me also think again at the affirmation of LeakedSource that VerticalScope might store all data in a single place.
While this is technically not impossible, I seriously doubt that they invested so much work in consolidating user accounts into a single database.
As a conclusion, there are many things in the LeakedSource posting that simply don’t make too much sense if you see the big picture.

You must be logged in to post a comment.