I am having troubles with Twitter… They have suspended my account @sorinmustaca and there is no way I can get it back.
Also the @it_securitynews is being constantly blocked, but I can unblock it.
Background:
If you read the news, you may have heard that Twitter is closing millions and millions of accounts.
According to this article in Washington Post, Twitter suspended more than 70 million accounts in May and June, and the pace has continued in July.
The rate of account suspensions, which Twitter confirmed to The Post, has more than doubled since October, when the company revealed under congressional pressure how Russia used fake accounts to interfere in the U.S. presidential election. Twitter suspended more than 70 million accounts in May and June, and the pace has continued in July, according to the data.
What does this have to do with me and my suspended account?
My account is used to publish the news from IT Security News – www.itsecuritynews.info and everything is done automatically.
This seems to trigger some automatic mechanisms, which signal Twitter to block my accounts.
However, there is a bug in their blocking page.
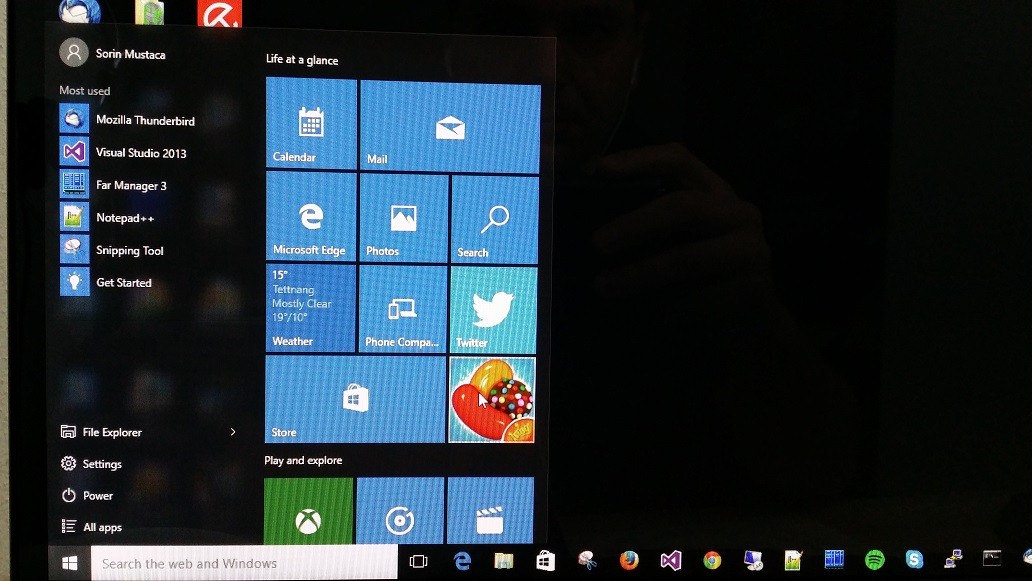
If you try to login into a suspended account, you end up in a loop, which basically prevents you to do anything else with twitter.com.
The only solution is to manually erase the cookies and start fresh with another account.

Shame on you Twitter!

You must be logged in to post a comment.