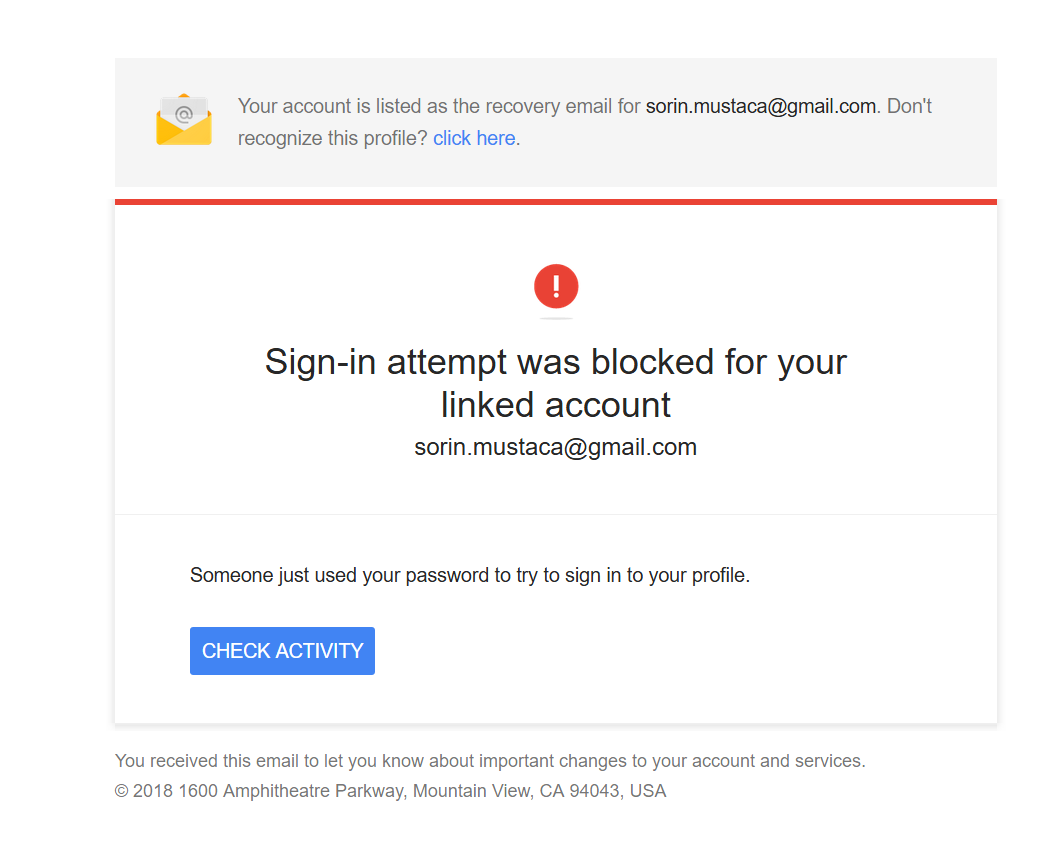
The email below looks like a classical phishing trying to fool users to enter their details and get access to the Google account.
But, if you check it, you will be redirected in two steps to an online Canadian pharmacy website.

I wonder why so much trouble for a stupid Canadian pharma website?
Do people still buy from these crappy websites ?
© Copyright 2018 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca - Security & Technology
Interested in professional consulting on this topic?
Check Endpoint Cybersecurity to see the consulting services we offer.
You must be logged in to post a comment.